Your CISO has a Quantum deadline. Your CIO doesn’t.
The cryptographic threat doesn't require a working quantum computer to be real. It requires only the expectation of one in the future, plus an adversary patient enough to record encrypted traffic now
Disclaimer: I am not a Quantum expert. I set out to ask one question.
What should an Enterprise Leader pay attention to when we hear the word Quantum and the first word that comes to mind is.... HYPE?
Bookmark this so you can reference it as needed!
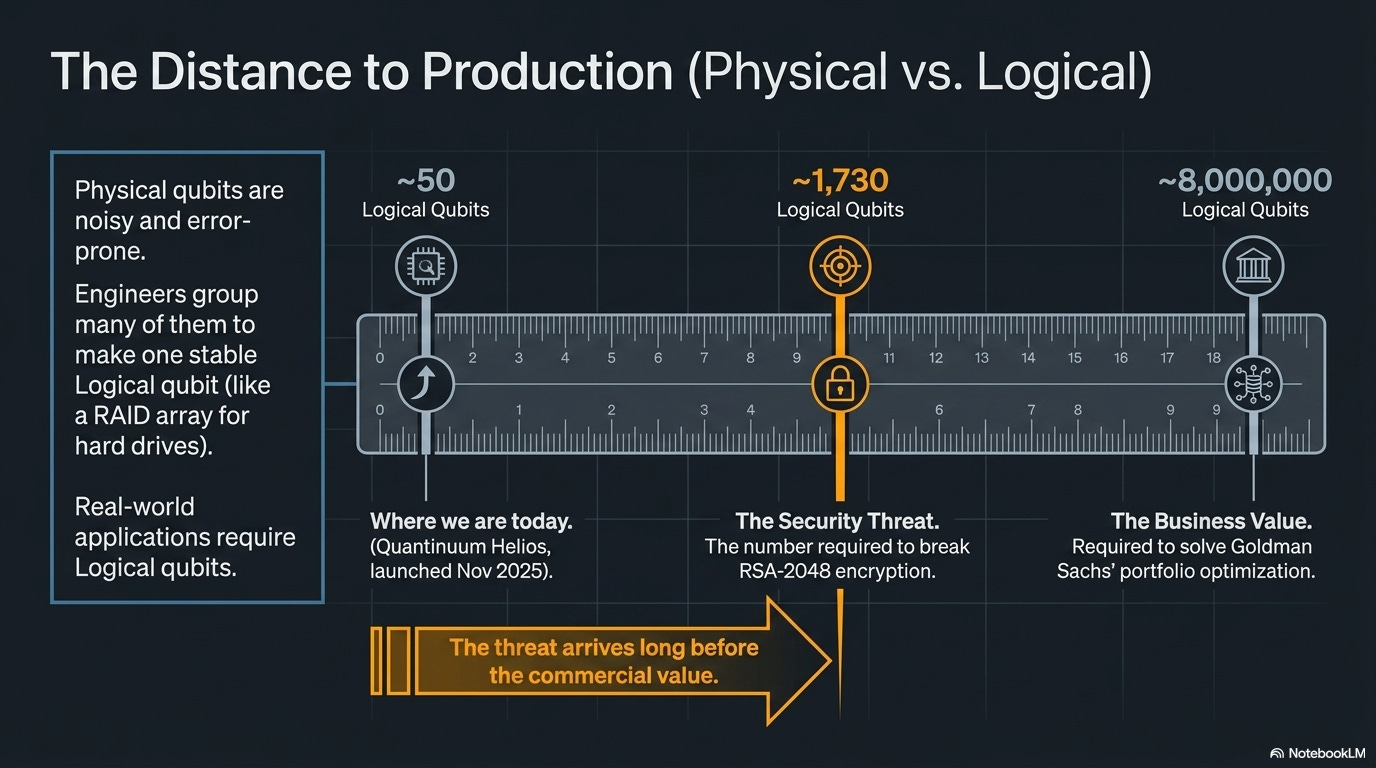
In 2025, Goldman Sachs quietly dismantled its quantum-computing team. The internal post-mortem, surfaced by Bloomberg in April 2026, was unsentimental: the portfolio-optimization problem the team was chasing would need roughly 8 million logical qubits to deliver a real edge over classical methods. The most accurate quantum computer on the market today, Quantinuum’s Helios (launched November 2025), has 98 physical qubits and roughly 50 error-detected logical qubits.
Goldman did the math and reallocated.
ELI5: Physical vs. logical qubits
Qubits are the quantum version of bits, but they’re noisy and error-prone. So engineers gang lots of “physical” qubits together to make one stable “logical” qubit, the way a RAID array uses many disks to look like one reliable drive. Today’s best machine has ~50 logical qubits. Breaking RSA-2048 needs roughly 1,730. Cracking Goldman’s portfolio problem needs ~8 million.
JPMorgan, which has run quantum projects for years, kept investing. They co-authored a Nature paper in March 2025 demonstrating certified quantum randomness on Quantinuum’s 56-qubit H2 system. They’re partnered with IBM on optimization. They’re hiring quantum algorithm researchers. They’re reading the same data Goldman read.
Both calls make sense once you see what each bank was actually asking.
Goldman asked, “can quantum beat our classical computers on this real problem today?” The answer was no, and won’t be for years probably, so they put the money elsewhere.
JPMorgan asked, “do we want to be ready when it can?” Their answer was yes, so they kept building muscle.
Same data, different question, opposite move. Both are fine.
Keep that split in mind as you read on. There are actually two quantum decisions to make in 2026, not one.
The first sits with your CISO: when do we swap out our encryption so quantum computers can’t break it later?
The second sits with your CIO: do we experiment with quantum now to find new business value?
Two different people own these calls, the timelines don’t line up, and the cost of getting each one wrong is very different.
The McKinsey 2026 Quantum Technology Monitor, which calls 2026 a “commercial tipping point” and projects $1.3T-$2.7T of value at stake by 2035, mashes them together. So do most of the boardroom slides this report is going to inspire.
I believe mashing them together is a mistake.
Here’s why from what I understand.
Understanding McKinsey’s “tipping point”
McKinsey is alone among Tier 1 analysts in calling 2026 the tipping point.
Forrester’s “State of Quantum Computing 2026” frames practical enterprise applications as 2030-likely.
Deloitte plans for 2030 scenarios.
IDC’s quantum guide treats 2029 as “strategic capability emergence.”
BCG, which projected $450B-$850B of quantum value by 2040 in its 2024 analysis, came back in October 2025 with a sharply more conservative $50B near-term industry-value figure.
QED-C (the consortium that actually counts revenue) sized the total quantum-computing market at $1.9B in 2025 and projects $3B by 2028.
McKinsey’s $1.3T-$2.7T-by-2035 is roughly three times BCG’s most-cited number, set five years earlier. It’s the high end of a wide credible range. That doesn’t make it wrong. It does make “tipping point” an optimistic claim, not consensus.
The investment numbers deserve a similar asterisk.
McKinsey reports $12.6 billion in 2025 quantum-tech investment, 6.3x 2024. The headline pulls in government grants, public-private co-funding (PsiQuantum’s Australian package alone topped $1B AUD), and broader quantum-technology funding beyond computing.
PitchBook’s narrower venture-only count for 2025 closes around $5-6 billion.
Both numbers tell the same direction-of-travel story. They answer different questions about magnitude.
Same with the customer count.
McKinsey’s “300+ enterprises actively engaged” is a curated list of flagship logos.
QED-C counts 7,418 quantum-engaged organizations worldwide.
The real picture isn’t 300. It’s that out of roughly 7,400 organizations doing something with quantum, McKinsey selected 162 for detailed analysis and identified roughly 300 with funded codevelopment partnerships. Engagement isn’t adoption.
Where McKinsey is genuinely useful is the structural pattern of who’s writing checks and who’s cashing them. Investment is now overwhelmingly private money. The public-and-government share of total quantum funding collapsed from roughly 33% in 2024 to about 3% in 2025. Governments stepped back; venture, corporate, and crossover funds stepped in.
The money is also concentrating. 60% of 2025 capital went into the top ten deals, and they tell you what’s actually being built:
IonQ bought Oxford Ionics for $1.075B (announced June 9, 2025, closed September 17, 2025). Almost all stock, ~$10M cash. IonQ were buying trapped-ion chip expertise and a roadmap to 2 million physical qubits (about 80,000 logical) by 2030. This was talent and IP acquisition, not market consolidation.
PsiQuantum raised a $1B Series E in September 2025, led by Nvidia and BlackRock. The money is going into actual real-estate. They’re constructing fault-tolerant quantum-computing facilities in Brisbane (partial operation by 2027) and Chicago (broke ground March 2026), targeting ~1 million physical qubits by 2029.
Xanadu went public via SPAC. The capital is going into scaling photonic-qubit hardware and cloud access through their Borealis system.
IBM committed to its Starling roadmap publicly in June 2025. The spend goes into Poughkeepsie fabrication: a chip-by-chip path (Heron, Flamingo, Loon, Kookaburra, Cockatoo) toward 200 logical qubits by 2029, then Blue Jay at 2,000 logical qubits by 2033+.
Quantinuum launched Helios commercially in November 2025. Their spend is on trapped-ion hardware refinement (98 physical qubits, 50 error-detected logical, 99.921% two-qubit gate fidelity) and on the cloud-access business that lets banks and pharma run jobs without buying a machine.
Pasqal sold a system to Aramco in Saudi Arabia and is building toward 200 logical qubits by 2030. Capital is funding neutral-atom hardware iteration plus international deployment.
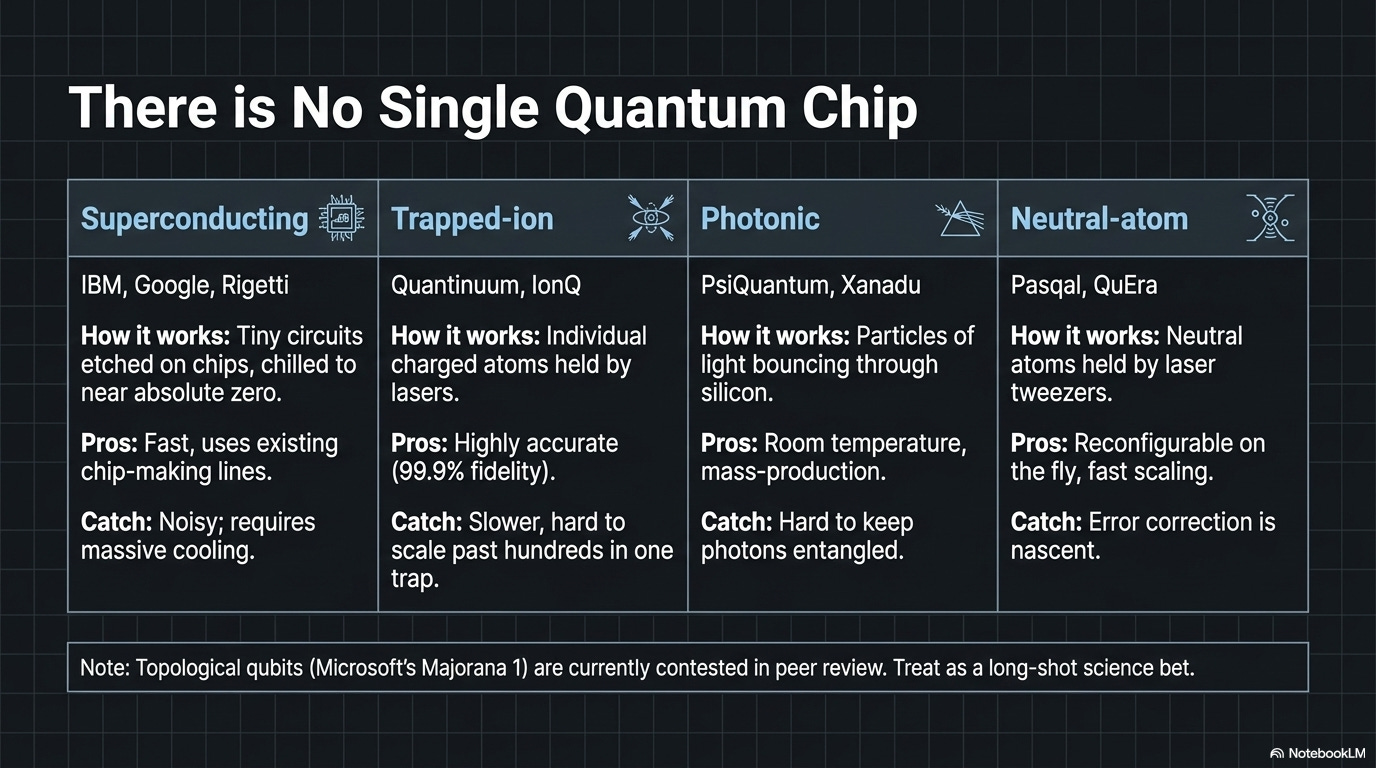
ELI5: The four kinds of qubits these companies are building
There’s no single “quantum chip.” Different companies are betting on different physics for how to make a qubit. Each approach has tradeoffs in speed, error rate, scale, and how much it costs to keep the thing cold.
Superconducting qubits (IBM, Google, Rigetti). Tiny circuits etched on a chip, chilled to near absolute zero (-273°C) inside a giant fridge. Fast, well-funded, easiest to scale on existing chip-making lines. The catch: they’re noisy, so you need lots of physical qubits to get one logical one.
Trapped-ion qubits (IonQ, Quantinuum, Oxford Ionics). Individual charged atoms held in place by lasers and electromagnetic fields, then nudged with more lasers. Very accurate (Quantinuum just hit 99.921%), but slower than superconducting. Hard to scale past hundreds of qubits in one trap.
Photonic qubits (PsiQuantum, Xanadu). Use particles of light bouncing through silicon waveguides at room temperature. The dream is no fridge needed and easy mass-production using semiconductor fabs. The catch: photons are hard to keep entangled long enough to compute.
Neutral-atom qubits (Pasqal, Atom Computing, QuEra). Like trapped-ion but with electrically neutral atoms held in place by laser tweezers. Reconfigurable on the fly, scaling fast (already past 1,000 atoms in some systems), but error correction is still being figured out.
There’s also topological qubits (Microsoft’s Majorana 1 bet). Theoretically much more error-resistant, but the underlying physics is now contested in peer review. Treat as a long-shot science bet.
Bottom line: nobody knows which approach wins. That’s why money is splitting across all of them.
What’s the money actually buying?
Three things, mostly:
silicon and atom-trap hardware (IBM, Quantinuum, IonQ, Pasqal, Atom Computing)
fabrication and lab buildings (PsiQuantum, IBM Poughkeepsie)
quantum algorithm researchers.
Almost no one is buying for revenue, because there isn’t much revenue yet. QED-C sized the entire quantum-computing market at $1.9B in 2025.
Inside customer enterprises, the spend pattern is different.
33% of analyzed companies are spending $10M+ a year on quantum.
7% are spending over $50M.
The biggest single corporate budget reported is $200M.
Most of that money flows back into the same vendor list above, mainly through cloud quantum services (AWS Braket, Azure Quantum, IBM Quantum, NVIDIA’s CUDA-Q), with a small slice going to in-house quantum algorithm teams.
That’s serious capital, and serious capital is the right answer for where we are. Real labs, real chips, real talent, real cross-vendor learning, all compounding at the same time. This is exactly what early-stage breakthrough technology should look like when it’s working. The companies writing these checks are buying themselves the option to be ready, the IP that comes from building, and the relationships that come from doing it alongside the best researchers in the field. All of that is valuable on its own, before any single deployed system shows up.
The only thing worth keeping clear in your head: “we’re funding research and learning” and “we have a quantum computer running production work” are two different sentences, and 2026 is squarely in the first one.
That’s not a problem. That’s the stage of the curve we’re at, and that’s the stage that deserves the investment.
The buried lede: cryptography is the only timeline that’s already started
McKinsey covers cybersecurity in a 5-page deep-dive starting on page 73. For everyone reading this who isn’t running a quantum innovation budget, that section deserves to be on page 1.
The cryptographic threat doesn’t require a working quantum computer to be real. It only requires the expectation of one in the future, plus an adversary patient enough to record encrypted traffic now and decrypt it later. The phrase is “harvest now, decrypt later.”
Nation-state collection programs assume it.
Insurance contracts protecting underwriting data for decades assume it.
Mortgages that need to remain confidential for 30 years assume it.
ELI5: Harvest now, decrypt later (HNDL)
A foreign intelligence service doesn’t need a quantum computer today to read your traffic. They just copy the encrypted stuff now and stash it. When quantum computers eventually get good enough, they go back and decrypt the old recordings. Anything that needs to stay secret for 20-30 years (life insurance files, mortgages, M&A docs, intelligence) is already at risk.
The reason this got much more urgent in 2025 is one paper. Craig Gidney, in May 2025, published a follow-up to the canonical Gidney-Ekerå 2019 estimate. The 2019 paper required 20 million noisy qubits to factor 2048-bit RSA in 8 hours. The 2025 paper drops the requirement to under 1 million noisy qubits (roughly 1,730 logical qubits) running in under a week (arXiv:2505.15917). A 20x reduction in the qubit cost of breaking RSA in six years, driven by algorithmic improvements, not hardware.
ELI5: Why RSA is the target
RSA is the math protecting almost everything online: banking, email, secure websites, iMessage, mortgages. It works because multiplying two huge prime numbers is easy but factoring the result back is supposedly impossible. A big enough quantum computer can do that factoring. Once it can, the lock isn’t a lock anymore. Gidney’s 2025 paper said the lock can be picked with 20x less hardware than we thought.
While at MIT last week, I happened to walk by Professor Robert Rivest - the R in RSA! How cool?
The Global Risk Institute’s 2025 Quantum Threat Timeline (Mosca/Piani, March 2026) registered the move. Expert assessment of a cryptographically-relevant quantum computer arriving within 10 years jumped from 34% in 2024 to 28-49% in 2025. That’s the largest single-year shift in the report’s seven-year history. Within 15 years: 51-70%.
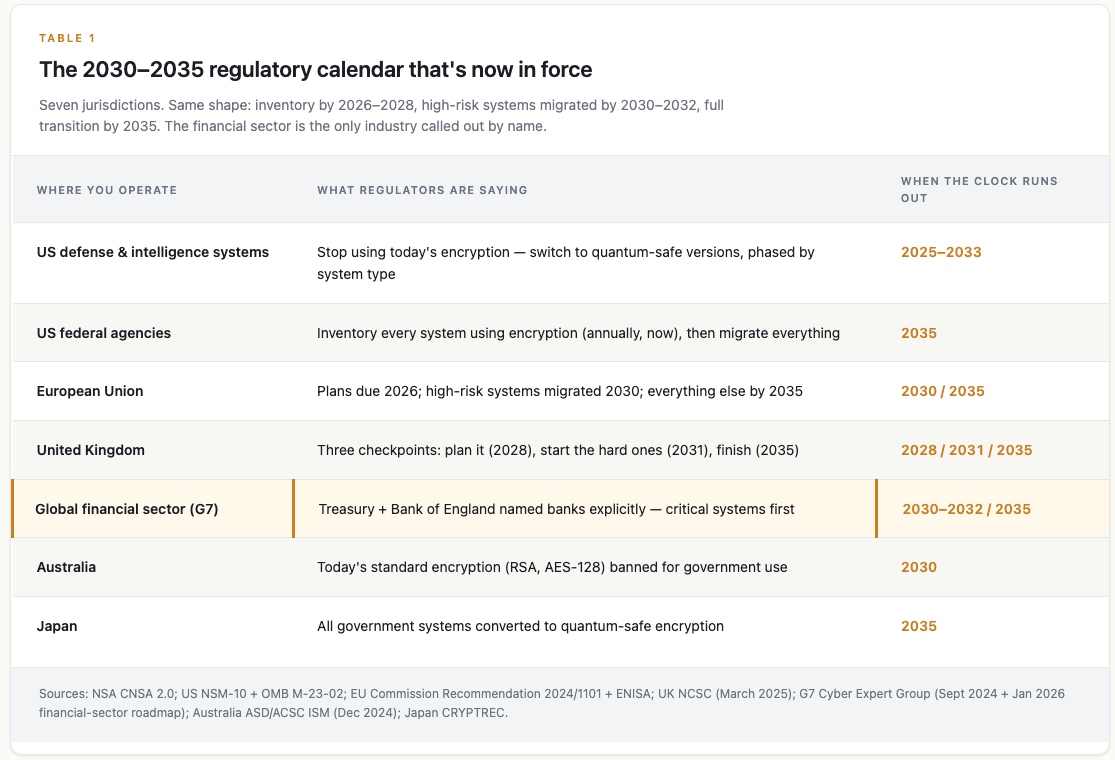
Against that math, here’s the regulatory calendar that’s now in force:
Sources: NSA CNSA 2.0; US NSM-10 + OMB M-23-02; EU Commission Recommendation 2024/1101 + ENISA; UK NCSC (March 2025); G7 Cyber Expert Group (Sept 2024 + Jan 2026 financial-sector roadmap); Australia ASD/ACSC ISM (Dec 2024); Japan CRYPTREC.
The G7 Cyber Expert Group line is the one financial-services leaders should be highlighting. Co-chaired by US Treasury and the Bank of England, the September 2024 statement and January 2026 financial-sector roadmap explicitly name the financial sector and put 2030-2032 as the critical-systems milestone, with 2035 as the outer planning horizon. That’s not an industry think-tank slide. It’s a coordinated G7 cyber-policy commitment with Treasury and BoE press releases attached.
The migration costs are starting to surface too. GAO-25-108590, published June 2025, cited an OMB estimate of $7.1 billion just to migrate U.S. federal civilian systems to post-quantum cryptography (PQC) — the new generation of encryption designed to withstand quantum attacks. That’s one country, executive branch only. No DoD, no private sector. Multiply across 30 G7 + G20 economies and the public-sector spend alone runs well into the hundreds of billions over the migration window.
ELI5: PQC and the new NIST algorithms
PQC stands for “post-quantum cryptography.” It’s the next-generation lock that quantum computers can’t pick.
NIST (the US standards body) ran a global competition to find replacements and in August 2024 finalized three:
1. ML-KEM for exchanging keys,
2. ML-DSA for digital signatures, and
3. SLH-DSA as a backup signature scheme.
These are the algorithms enterprises actually swap to.
The vendor world has caught up faster than most people realize. NIST finalized FIPS 203 (ML-KEM), FIPS 204 (ML-DSA), and FIPS 205 (SLH-DSA) on August 13, 2024. Those are the algorithms enterprises actually need. (FIPS 206, derived from Falcon, remains in draft as of May 2026.)
Apple shipped PQ3, the post-quantum protocol for iMessage, in iOS 17.4 on February 21, 2024.
Mastercard has been shipping quantum-resistant Enhanced Contactless cards through Giesecke+Devrient and Thales since April 2024.
SWIFT has publicly committed that SwiftNet 8.0, scheduled for 2027, will be PQC-enabled.
The BIS Innovation Hub’s Project Leap Phase 2, published December 11, 2025 with the Bank of England, Banca d’Italia, Bank of France, Bundesbank, Nexi-Colt, and SWIFT, tested ML-DSA signatures at the ISO 20022 Business Application Header layer and measured a 12.9x signature-size growth (256 bytes to 3,293 bytes).
There is no “wait for the standards” excuse anymore. Standards exist. Products ship. Central banks are running test traffic.
Here’s the part CIOs can’t afford to ignore: picking the wrong replacement encryption is expensive.
In July 2022, the SIKE family of post-quantum candidates (through round 4 of NIST’s process) was broken classically. The Castryck-Decru attack ran in roughly 62 minutes on a single CPU core of a 2.6 GHz Xeon. Not a supercomputer. One core, one hour, one paper.
That’s the design assumption: the algorithms you migrate to today may not be the algorithms you settle on by 2035. Plan for at least one mid-migration swap.
What’s real on the value-creation side, and what isn’t
Now to the other half of McKinsey’s case — the value-creation story.
Real quantum-classical hybrid pilots are running.
JPMorgan’s certified-randomness work with Quantinuum was published in Nature in March 2025, a genuine first-of-kind protocol demonstration.
HSBC and IBM published a press release in September 2025 claiming the first quantum-enabled algorithmic-trading workflow, with up to 34% improvement on a backtest of 1.1 million historical bond-trade requests.
AstraZeneca, IonQ, AWS, and NVIDIA presented a 20x speedup on a Suzuki-Miyaura reaction simulation at ISC High Performance in June 2025.
Aramco deployed Pasqal’s quantum computer in Saudi Arabia.
BMW with Classiq and NVIDIA is optimizing electrical and mechanical architectures.
Q-CTRL is reporting commercial advantage in GPS-denied quantum sensing for navigation. Narrow, but the closest thing to recurring revenue from quantum I can find.
These are real results. They’re not the same thing as deployed enterprise capability. Here’s the honest assessment on the three highest-profile pilots:
JPMorgan + Quantinuum certified randomness is a peer-reviewed Nature paper. Scott Aaronson’s assessment, on his blog the week the paper appeared, was that the protocol works but isn’t yet practical because verification is “basically as expensive as spoofing the results.” A demo that works, not a product aready to market.
HSBC + IBM bond trading is a vendor-co-authored press release, not peer-reviewed. The 34% improvement is measured against a backtest, not a deployed classical baseline in production. HSBC has not stated production deployment.
AstraZeneca + IonQ drug discovery is a conference presentation, not peer-reviewed. The 20x speedup is benchmarked against a prior quantum implementation, not a production classical workflow. No drug, no candidate molecule, no revenue.
I went looking for a single publicly documented case of a quantum computer producing measurable revenue or cost savings in a deployed enterprise workflow in 2025-2026.
I didn’t find one.
Every “first commercial application” claim is either a vendor-co-authored research demonstration, a backtest on historical data, or a benchmark against a prior quantum implementation.
The cybersecurity half of the case is fully supported. The enterprise-value-creation half is, if anything, understated.
The hardware roadmaps are credible and improving.
IBM’s June 2025 update committed to Starling, targeting 200 logical qubits and 100 million quantum operations by 2029, with Blue Jay at 2,000 logical qubits by 2033+.
IonQ’s post-Oxford Ionics roadmap targets 2 million physical qubits (about 80,000 logical) by 2030.
Quantinuum’s Helios system, launched November 2025, hit 99.921% two-qubit gate fidelity on 98 physical qubits, with 50 error-detected logical qubits.
Google’s Willow chip, announced December 2024, was the first sub-threshold demonstration of surface-code error correction (Nature, January 2025).
Microsoft’s Majorana 1 announcement in February 2025 is a separate story, and the kind of thing that should make any enterprise leader cautious about taking vendor roadmaps at face value. The Nature paper carried an editor’s note clarifying that the data did not represent evidence of Majorana zero modes. Independent physicists publicly contested the claim in Nature, Science, and Physics World in March 2025. Allegations of data manipulation in the foundational 2018 paper resurfaced.
The most-hyped “topological qubit” roadmap in the field is, charitably, contested.
The public-equity tape tells its own story. IonQ dropped 39% in a single day in early 2025 after Jensen Huang’s “15 to 30 years” comment. Rigetti dropped 45%. D-Wave currently trades at roughly $10B market cap on $24M trailing revenue. Not a tipping-point multiple by any conventional measure. If the market believed McKinsey’s 2026-tipping-point framing, those tapes would look different.
If you’re in one of the industries where quantum is already showing real (if narrow) results — drug and materials research, financial portfolio and risk modeling, logistics routing, chemical catalyst design, security-grade randomness, or GPS-free navigation for defense, energy, and self-driving systems — and your direct competitors are already building with quantum vendors, then it’s worth keeping a seat at the table. McKinsey’s pitch (that the cost of waiting is non-linear because IP, talent, and access are all consolidating) is a fair argument for innovation budgets at firms that already have a strategic R&D function.
If your enterprise doesn’t sit inside one of those clusters, the value-creation story is mostly aspirational marketing for the next 5-10 years. That’s not me saying it. That’s Forrester saying it. That’s BCG saying it (after revising downward). That’s Goldman’s 8-million-qubit memo saying it.
McKinsey says “could be at an inflection point” themselves, on page 28: could. Not “is.”
The financial services twist: three pressures hitting at once
Insurance, banking, and asset management are stuck in a bind that most other industries don’t face. Three things are landing on them at the same time.
One: long-lived sensitive data.
A 30-year mortgage. A whole-life insurance policy with claims data covering 50-70 years. An annuity contract. A trust beneficiary’s full financial history. Documents that need to remain confidential past the timeline at which a fault-tolerant quantum computer becomes plausible.
Harvest-now-decrypt-later doesn’t hit every industry equally. It hits hardest where the data has to stay secret for a long time. Healthcare records have similar shelf life (HIPAA files often live 50+ years), but no regulator has called healthcare out by name yet.
Two: explicit regulatory naming, and earlier than people realize.
The Monetary Authority of Singapore was first off the line. MAS Circular MAS/TCRS/2024/01, issued February 21, 2024 to FI CEOs personally, named “the cybersecurity risks associated with quantum” and listed three explicit asks: monitor developments, build a cryptographic asset inventory, uplift staff competencies. First major regulator to put quantum on the CEO’s desk by name.
The G7 Cyber Expert Group’s September 2024 statement and January 2026 financial-sector roadmap put 2030-2032 as the critical-systems milestone with 2035 as the outer planning horizon, financial sector named explicitly.
The OCC’s Fall 2024 Semiannual Risk Perspective added PQC to the emerging-risk list and reiterated it in July 2025.
The Bank of England’s October 2025 paper on innovation in AI, DLT, and quantum confirmed the BoE is building post-quantum risk scenarios and piloting supervisory briefings.
The Hong Kong Monetary Authority‘s Fintech 2030 announcement (November 3, 2025) committed to a Quantum Preparedness Index for HK banks. It’s the first time a regulator has built an actual yardstick for measuring how ready banks are.
NYDFS Part 500 § 500.15 doesn’t name quantum specifically, but its industry-standard-encryption and crypto-agility expectations point in the same direction.
The EU’s DORA technical standards, effective January 2025, require regulated entities to manage “cryptographic ageing” (implicit PQC capture).
The notable gap: the National Association of Insurance Commissioners (NAIC), which coordinates the US state-based insurance regulators, has not issued PQC-specific guidance (that I can find). State insurance regulators are silent so far.
When the prudential and conduct regulators move, the insurance side eventually follows, and it usually takes another 12-24 months. This is the gap that will close by examination cycle 2027-2028.
Three: payments-rails interdependence.
Every payment rail — credit and debit cards, ACH (the system that moves your direct deposit and bill pay), wire transfers, and the SWIFT/ISO 20022 messaging that banks use to talk to each other internationally — runs on encryption owned by someone else. Card networks, central banks, and global standards bodies all set the rules, and they move slower than any individual bank.
Specifically: chip cards (the EMV standard) use RSA and elliptic-curve encryption to authenticate every transaction; ACH and wire transfers ride on TLS (the same lock that protects your web browser), which is exposed to harvest-now-decrypt-later; SWIFT and ISO 20022 messages between banks are signed with RSA-2048 at the header layer (the same layer the BIS Project Leap pilot just tested with the new PQC signature standard, ML-DSA); and the secure key vaults inside card networks (HSMs) still use older algorithms like Triple-DES, AES, and RSA. All of those have to migrate in a coordinated way, or the rails break.
ELI5: The acronym soup
ACH — Automated Clearing House. The plumbing behind direct deposit, bill pay, and most US bank-to-bank transfers.
SWIFT — the global messaging network banks use to send international payment instructions to each other.
ISO 20022 — the modern format SWIFT messages are written in. Think of it as the standard envelope all bank messages now use.
EMV — the chip-card standard (the “E” was Europay, with Mastercard and Visa). It’s why every card reader now expects you to insert or tap, not swipe.
TLS — Transport Layer Security. The padlock in your browser. Also protects most bank-to-bank traffic.
HSM — Hardware Security Module. A tamper-resistant box that stores a bank or card network’s most important encryption keys.
RSA / ECDSA / ECC / Triple-DES / AES — the specific encryption recipes in use today. The first three are the ones quantum computers will eventually break.
ML-DSA — one of the three new NIST post-quantum standards (finalized August 2024). The replacement digital-signature recipe.
Financial services leaders don’t get to migrate alone. They have to coordinate with networks they don’t control. That extends the timeline and increases urgency at the same time, which is a rare and uncomfortable combination.
Mastercard moved early. Productized quantum-resistant contactless cards have been shipping since April 2024 through Giesecke+Devrient and Thales, on the EMVCo-backed Enhanced Contactless spec announced in 2021. SwiftNet 8.0, scheduled for 2027, will be PQC-enabled.
Visa is researching, more quietly. Project Leap Phase 2 demonstrated PQC at the central-bank layer in December 2025.
Liberty Mutual is one of the 300+ named in the McKinsey monitor, the highest-profile US insurer in the cohort.
Lloyd’s of London has flagged quantum as a systemic cyber risk that aggregates across portfolios. That’s the cleanest London-market acknowledgment that this is a class of risk, not a one-firm problem.
Beazley, Chubb, and Munich Re have begun including post-quantum protections in cyber-insurance offerings, visible publicly through the Google Cloud Risk Protection Program.
The cyber-insurance underwriting question (how do we price PQC readiness as a risk factor?) is going to land on actuarial desks before it lands on most CISOs’, the way MFA did in 2021-2022.
PQC readiness will become an underwriting question before it becomes a regulatory rule.
3 Actions for Enterprise Leaders in 2026
For most enterprises (not pure-play tech, not national security, not pharma R&D), these are the three moves that survive a hard sanity check.
1. Cryptographic inventory. This quarter.
You can’t migrate what you can’t see. The first deliverable of every credible PQC program is a cryptographic bill of materials:
where RSA-2048 is used
where ECC-256 is used
where TLS 1.2 endpoints are
which certificates expire when
what HSMs sit behind which apps
which third-party SaaS vendors handle your encrypted-at-rest data
what algorithms they’re using
which embedded systems shipped in the last decade have hardcoded crypto, etc.
This is the explicit ask in MAS’s February 2024 circular. It’s the explicit ask in OMB M-23-02: annual cryptographic inventory due to the Office of the National Cyber Director and CISA every year through 2035.
It’s the foundational dimension of every quantum-resilience assessment framework I’ve seen.
And most large enterprises think they have one but don’t. They have a CMDB and a TLS scan and a vague sense that “the security team handles cryptography.”
A real crypto inventory is a multi-quarter, cross-functional effort that surfaces the long tail of embedded, hardcoded, or vendor-controlled crypto.
ELI5: SHA-1
SHA-1 is one of those background pieces of crypto that signs and fingerprints digital things — software updates, certificates, document signatures. By the mid-2000s, researchers showed it could be faked. The industry agreed it had to go. It still took banks more than five years to actually rip it out of every system that used it — because it was buried inside vendor software, old certificates, custom code, and configurations nobody had touched in a decade. The PQC migration is bigger.
Banks took longer than five years to retire SHA-1. The 2030-2035 deadlines look generous until you do the math on a five-year migration window of every cryptographic dependency across an enterprise. That’s fast.
2. Cryptographic agility, not a one-time PQC swap.
ELI5: Cryptographic agility
Build your systems so you can swap out one encryption algorithm for another without rebuilding the system. Most legacy software has crypto algorithms hardcoded deep inside. That’s bad. When an algorithm gets broken (which has happened), you need to rip and replace. Agility means treating crypto like a plug-in, not a foundation.
The design assumption is that the algorithms you migrate to today may not be the algorithms you settle on by 2035. SIKE was a NIST round-4 candidate when Castryck and Decru broke it on a single CPU core in roughly 62 minutes in July 2022. Microsoft’s most-promoted hardware bet of 2025, Majorana 1, is now contested in peer review. The industry’s track record on betting big on a single primitive is not great.
In practice: build pluggable cryptographic interfaces. Make cryptographic agility a procurement requirement of every vendor that touches identity or data-in-transit. Treat PQC like TLS-version management, not a one-shot platform upgrade. The BIS Project Leap pilot in December 2025 found that the new quantum-safe signatures are roughly 13× larger than today’s. That’s your warning. The knock-on effects — more bandwidth used, slower transactions, bigger certificate stores, harder work for the secure-key boxes (HSMs) — are real. Model them before you migrate, not after.
3. Quantum-compute optionality without overcommitting.
For the value-creation lane, the move that pencils out for most enterprises is quantum-as-a-service through the hyperscaler you already use. AWS Braket, Azure Quantum, IBM Quantum, NVIDIA’s CUDA-Q. Hybrid workflows without buying a dilution refrigerator. McKinsey’s data shows private companies overwhelmingly access quantum through cloud providers; only public-sector and pure-play research orgs are buying on-premise hardware.
Set a hard cap. McKinsey’s median quantum-computing budget for industry players is $5-10M a year. For most enterprises that aren’t in the five-or-six hot use-case clusters, $1-2M annually for an exploration team that runs hybrid pilots and watches the technical roadmap is plenty. The optionality is real; the urgency is not. Goldman walked away from $8M-logical-qubit problems and reallocated. JPMorgan stayed in because their problem set sits closer to today’s hardware curve. Both calls are right because the questions are different. Don’t let an investor pitch turn an optionality bet into a balance-sheet line item.
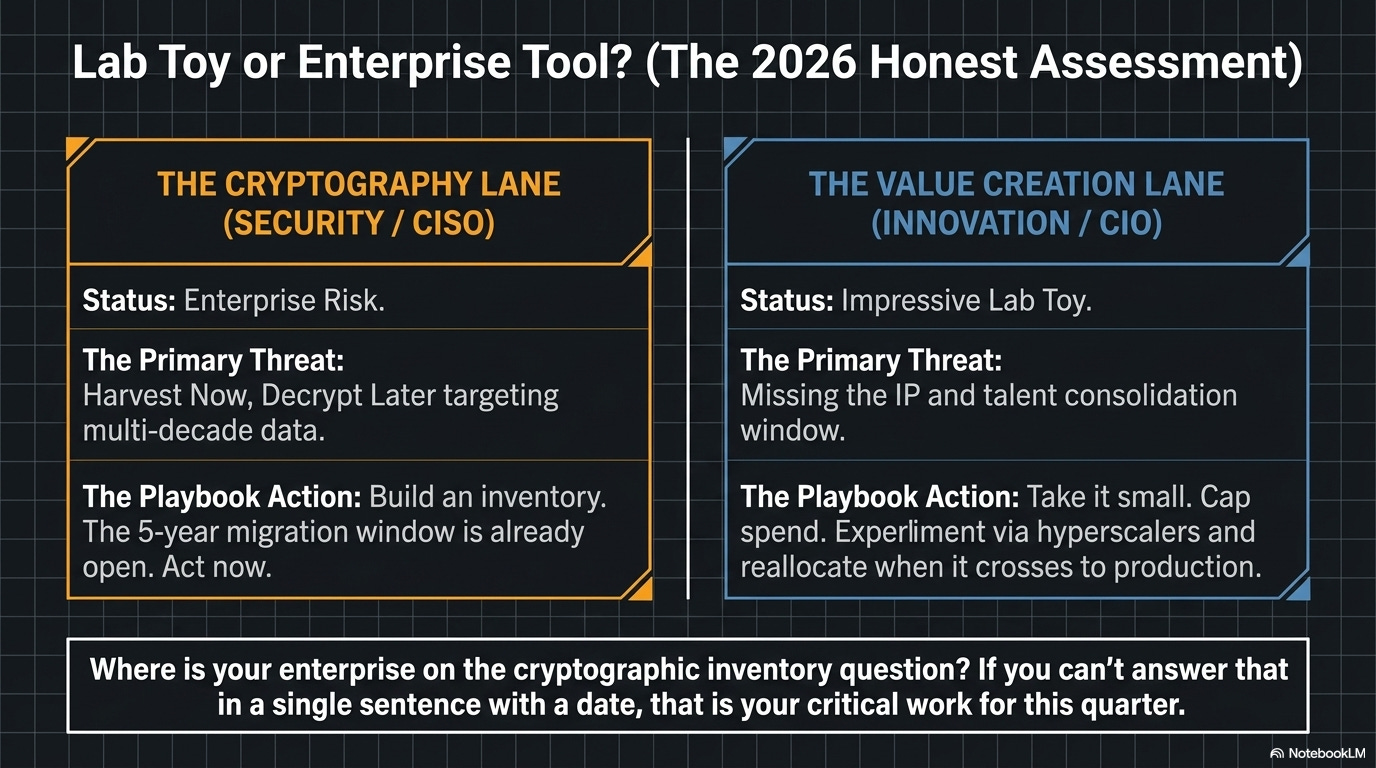
The honest line: lab toy or enterprise tool?
Both. Different lanes.
For the cryptography lane, quantum has already crossed from research curiosity into enterprise risk. The threat doesn’t require a working fault-tolerant quantum computer. Gidney’s May 2025 paper makes that math sharper than it’s ever been. The G7 has named 2030-2032 as critical for financial systems. NSM-10 names 2035 federal-wide. UK NCSC names 2028, 2031, 2035 in three phases. Australia names 2030. Mastercard already ships. SWIFT commits to 2027. BIS has run real test traffic at the central-bank layer.
The five-year migration window already opened.
For the value-creation lane, quantum is a cluster of impressive hybrid pilots, a handful of credible co-development partnerships, a $12.6B (or $5-6B, depending on the count) investment year that’s more about positioning than deployed revenue, and a “tipping point” framing that exactly one Tier 1 analyst is using for 2026. Whether the bet pays out in 5, 10, or 20 years is the question every roadmap dodges. Goldman read the dodge and walked. JPMorgan read it and stayed in. Both are right, because they’re answering different questions about different problems.
If you’re a CISO at a bank, an insurer, a hospital network, a critical-infrastructure operator, or any business with multi-decade data, quantum is your problem in 2026. Stop calling it a 2030 problem. The migration window already opened.
If you’re a CIO running an innovation budget at a firm in pharma, chemicals, finance, logistics, aerospace, defense, or energy, quantum is your option to take in 2026. Take it small, take it through the hyperscaler, set a $1-2M cap, andjust as with any innovation it’s easy to confuse activity with progress.
If you’re neither, quantum is a thing to track, not a thing to staff. The smart move is to read the McKinsey monitor and the Forrester forecast once a year, watch what JPMorgan and HSBC do with their hybrid pilots, watch what Goldman didn’t do, and reallocate when the technology actually crosses the gap from demonstration to production.
*Where is your enterprise on the cryptographic inventory question? If you can’t answer that in a single sentence with a date, that’s the work for this quarter.
Not the quantum optimization pilot.
References
Government / standards-body (Tier 0):
NIST FIPS 203/204/205 finalization — csrc.nist.gov
NSA CNSA 2.0 Cybersecurity Advisory + FAQ (Sept 7, 2022) — media.defense.gov
White House NSM-10 (May 4, 2022) — bidenwhitehouse.archives.gov
OMB M-23-02 (Nov 18, 2022) — whitehouse.gov
CISA/NSA/NIST joint factsheet — cisa.gov
UK NCSC PQC Migration Timelines (March 20, 2025) — ncsc.gov.uk
EU Commission Recommendation 2024/1101 — eur-lex.europa.eu
ENISA PQC Integration Study — enisa.europa.eu
G7 CEG September 2024 statement — home.treasury.gov
G7 CEG January 2026 Financial-Sector Roadmap — home.treasury.gov
Australian ASD/ACSC ISM — cyber.gov.au
GAO-25-108590 (June 2025) — gao.gov
MAS Circular MAS/TCRS/2024/01 (Feb 21, 2024) — mas.gov.sg
Bank of England innovation paper (Oct 15, 2025) — bankofengland.co.uk
HKMA Fintech 2030 (Nov 3, 2025) — hkma.gov.hk
BIS Project Leap Phase 2 (Dec 11, 2025) — bis.org
Vendor primary:
IBM Starling roadmap (June 10, 2025) — newsroom.ibm.com
Google Willow Nature paper — nature.com
Quantinuum Helios launch (Nov 5, 2025) — quantinuum.com
IonQ-Oxford Ionics close — ionq.com
Apple PQ3 — security.apple.com
JPMC + Quantinuum certified randomness (Nature, March 2025) — nature.com
Mastercard quantum-safe perspective — mastercard.com
Peer-reviewed / academic:
Gidney, “How to factor 2048-bit RSA integers with less than a million noisy qubits” (May 2025) — arXiv:2505.15917
Castryck & Decru, “An efficient key recovery attack on SIDH” (July 2022) — eprint.iacr.org
Quantinuum Helios technical paper — arXiv:2511.05465
Preskill, “Beyond NISQ: The Megaquop Machine” (2025) — preskill.caltech.edu
Industry / adversarial:
McKinsey Quantum Technology Monitor 2026 — mckinsey.com
Global Risk Institute Quantum Threat Timeline 2025 — globalriskinstitute.org
QED-C State of the Global Quantum Industry 2026 — quantumconsortium.org
Forrester “Practical Quantum by 2030 + Q-Day” — forrester.com
Bloomberg, Goldman walks / JPMorgan invests (April 2026) — bloomberg.com
IEEE Spectrum on Microsoft Majorana — spectrum.ieee.org
Aaronson on JPMC certified randomness — scottaaronson.blog
FS-ISAC PQC Working Group — fsisac.com