NVIDIA Builds the Factory Floor. RSA Sells the Fire Exits. They Need Each Other.
Two conferences, two weeks apart, one trillion dollars in the middle — and nobody can agree on how fast to spend it.
Two weeks ago, Jensen Huang stood on a stage in San Jose at GTC Conference and projected $1 trillion in AI infrastructure demand through 2027.
Last week in San Francisco, Kevin Mandia told an RSA crowd that “nobody’s ready for it.”
Both are right. Both are selling something.
That gap is going to define enterprise IT strategy for the next three years.
The easy narrative says these conferences represent opposing forces: NVIDIA wants you to build faster, security vendors want you to slow down. It’s a clean story. It’s also wrong.
The co-dependency nobody wants to admit
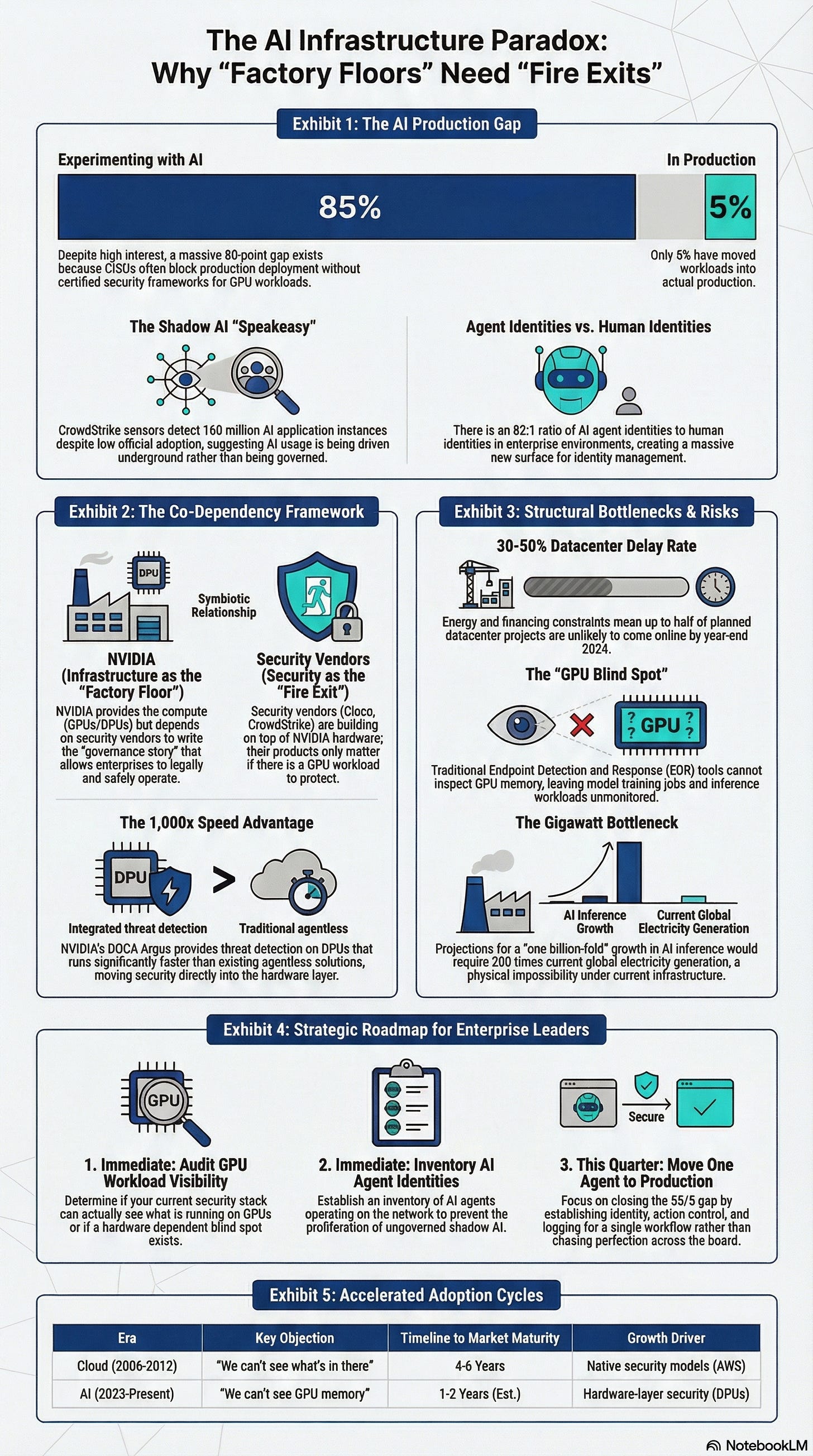
NVIDIA doesn’t just sell GPUs to the AI-first crowd. It showed up at RSA with DOCA Argus — runtime threat detection on BlueField DPUs that NVIDIA claims runs 1,000x faster than existing agentless solutions. Cisco, CrowdStrike, and Palo Alto Networks all build on NVIDIA hardware. The security vendors aren’t fighting NVIDIA’s infrastructure buildout. They’re building on top of it.
ELI5: BlueField DPUs — Think of a DPU as a dedicated bouncer at the door of a data center server. Instead of the main computer (CPU) wasting energy checking IDs and enforcing rules, the bouncer handles all the security and networking work independently. DOCA Argus is the bouncer’s playbook for spotting threats.
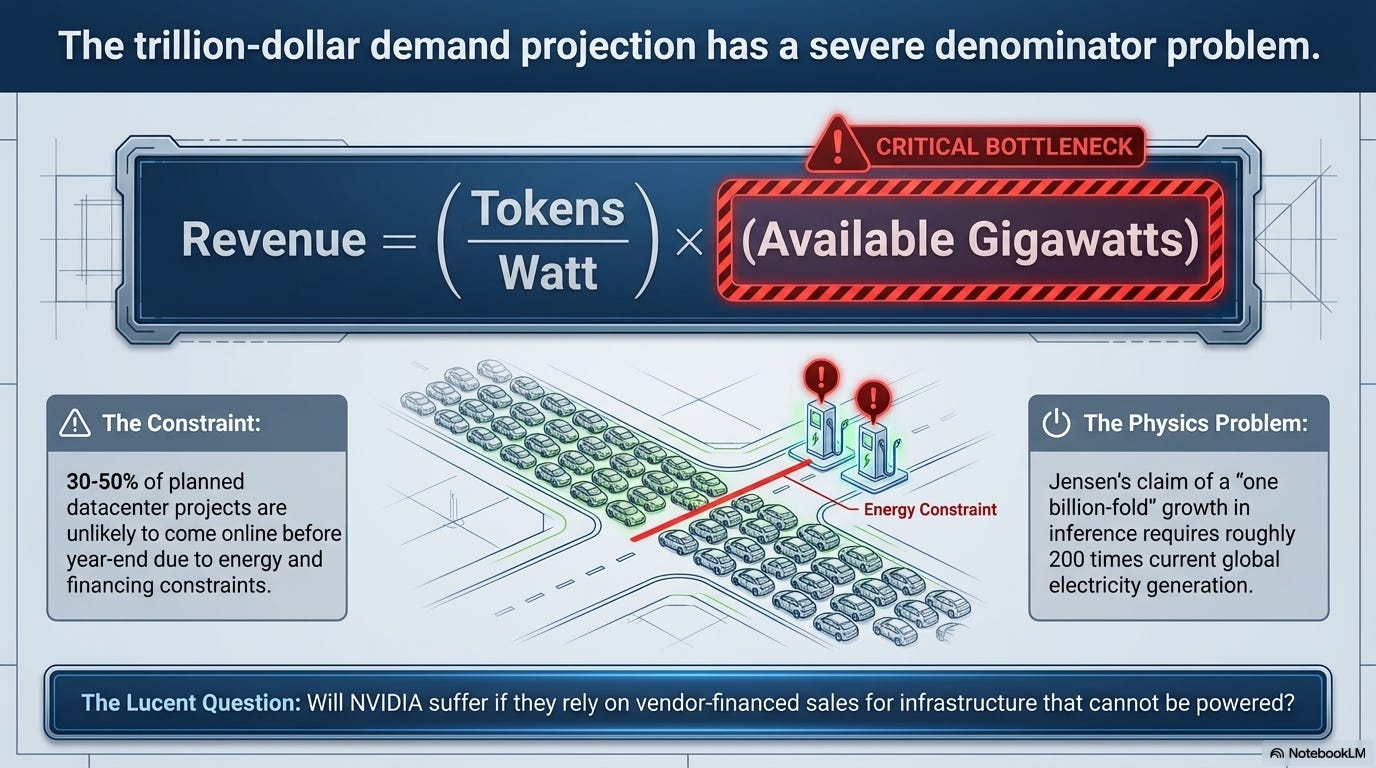
And NVIDIA needs security vendors just as badly. Jensen’s formula from GTC — Revenue = (Tokens per Watt) x (Available Gigawatts) — only works if enterprises actually deploy AI workloads at scale. Right now, they mostly aren’t.
Cisco’s survey puts it at 85% of major enterprises experimenting with AI agents and exactly 5% running them in production. The technology isn’t the problem. Companies can’t get it approved. CISOs won’t sign off on production deployment without a security story, and security vendors are the ones writing that story.
In practice: A financial services firm buys NVIDIA DGX systems to run fraud detection models. Without a security framework certified for GPU workloads, the CISO blocks production deployment. NVIDIA’s revenue depends on that CISO saying yes. The security vendor’s product only matters if there’s a GPU workload to protect. Neither makes money without the other.
NVIDIA builds the factory floor. Security vendors sell the fire exits. The factory doesn’t get an occupancy permit without fire exits. The fire exit business doesn’t exist without factories. They’re locked together.
The numbers that don’t add up (and what they tell us)
Pull two numbers from these same two weeks:
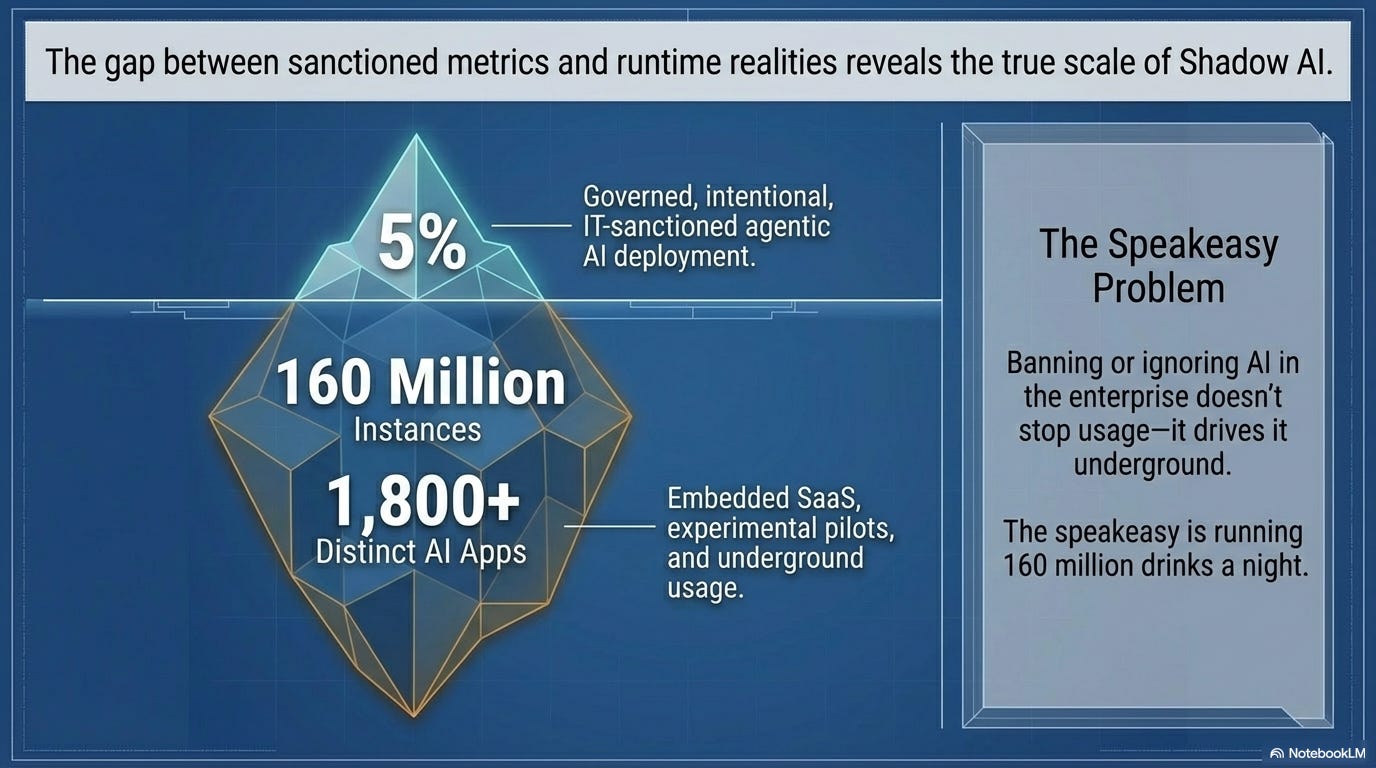
Cisco says 5% of enterprises have AI agents in production. CrowdStrike’s Falcon sensors detect 1,800+ distinct AI applications and 160 million instances across enterprise endpoints. How do you get 160 million instances of something that only 5% of organizations have deployed?
Unless you accept that these are measuring fundamentally different things. Cisco is counting governed, intentional, IT-sanctioned agentic AI deployment.
CrowdStrike is counting everything — shadow AI tools, embedded AI features in existing SaaS, personal accounts, and experimental pilots that nobody reported. Both are accurate and hence the problem.
This is the same dynamic we covered in the Speakeasy Problem: banning or ignoring AI in the enterprise doesn’t stop usage — it drives it underground. CrowdStrike just gave us the infrastructure-layer receipt. The speakeasy is running 160 million drinks a night.
Meanwhile, VentureBeat reports an 82:1 ratio of AI agent identities to human identities in enterprise environments. While 5 agent identity frameworks shipped at RSA, 3 critical gaps remain: agent-to-agent trust, memory integrity, and registry-to-runtime provenance. We’re building identity management for a workforce that outnumbers humans 82 to 1, and we haven’t figured out whether agents can verify each other’s credentials.
ELI5: Registry-to-runtime provenance — Imagine you register a new employee and give them a badge. Provenance means you can verify, at any moment, that the person using the badge is the same person you registered: not someone who copied the badge, modified their own permissions, or swapped identities with another employee. For AI agents, we can’t do that yet.
Have we seen this movie before?
The cloud computing era ran the same playbook, just slower. AWS launched in 2006 with no native security model. By 2010, the biggest enterprise objection to cloud was “we can’t see what’s in there.” Cloud security vendors barely existed. By 2012, the market was $4.1 billion. By 2026, cloud security is embedded in every enterprise stack and nobody thinks twice about it.
AI is running that same pattern at roughly 3-5x speed. The “GPU blind spot” — traditional EDR tools literally cannot see GPU workloads, creating an unmonitored attack surface in AI factories — is structurally identical to the cloud visibility problem of 2010. Futurum Group flagged this at RSA: 62% of organizations say AI-powered defensive tools are essential, while 62% have experienced significant increases in AI-driven attacks. Offense and defense are scaling together, on the same hardware, from the same vendor.
In practice: Your SOC team runs CrowdStrike on every endpoint. An attacker compromises a machine running an NVIDIA GPU workload — say, a model training job. CrowdStrike’s endpoint agent can’t inspect GPU memory. The attack runs undetected in the GPU layer. DOCA Argus is NVIDIA’s answer to that blind spot, but it only runs on BlueField DPUs, which means your existing security stack has a hardware dependency it didn’t have last year.
Think of NVIDIA as the casino. They built the floor, they supply the chips, and now they’re selling you the security cameras pointed at the players. The house doesn’t care whether you win or lose. It cares that you play. Jensen doesn’t need to pick a side. He owns the house.
What the vendor pitch decks aren’t telling you
Notice what NVIDIA now sells: the GPU, the DPU (BlueField), the security layer (DOCA Argus), the networking stack (Spectrum-X), and the agentic AI framework (OpenShell). When Cisco, CrowdStrike, and Palo Alto say they “build on NVIDIA hardware,” that’s not a partnership announcement. It’s a disclosure that they’ve acquired a hardware dependency they didn’t have two years ago. You’re not buying a multi-vendor security stack. You’re buying an NVIDIA-certified ecosystem with multiple logos on the box.
And DOCA Argus, NVIDIA’s answer to the GPU blind spot, only covers NVIDIA hardware. AMD MI300X workloads? Intel Gaudi? Still invisible. So you’re trading one blind spot for fragmented visibility — you can see threats on NVIDIA hardware but stay blind on everything else.
There’s also a harder question nobody at either conference answered: does any of this work? CrowdStrike’s detection of 1,800 AI applications across enterprise endpoints is a remarkable capability demo. But no RSA 2026 vendor showed measurable breach prevention or actual incident response improvement from agentic security tools. DOCA Argus claims 1,000x faster threat detection that is sourced entirely to NVIDIA, zero third-party validation. Before you make a security architecture bet on this stack, you’d want to know whether you’re buying proven protection or a very well-funded proof of concept.
The timeline is also not what the conference energy suggests. Sightline Climate estimates 30-50% of planned datacenter projects won’t come online this year due to energy and financing constraints. The factory floor in the headline metaphor is, for a meaningful slice of the market, still under permit review.
To be fair: none of this means the build-out is fake. Gartner projects $2.52 trillion in worldwide AI spending in 2026, up 44% year-over-year. The direction is right. But the co-dependency between NVIDIA and security vendors has a timing problem baked in — NVIDIA needs fast deployment to hit its numbers; governance frameworks slow deployment by design.
Every security gate a CISO adds to agent rollout is friction on the timeline. The two sides need each other, but they don’t need the same thing from the calendar.
What this means for enterprise leaders
Alex Stamos warned that “exploit discovery has gone exponential.” George Kurtz declared that “by 2027, your smartest employee will be a machine.” Up to 80% of reconnaissance and exploitation is now AI-driven. Google’s Mandiant team says attackers have reduced the defender intervention window to 22 seconds.
These aren’t reasons to stop deploying AI. They’re reasons to stop treating security as something we figure out after deployment.
The 85%/5% production gap is the most important number in enterprise AI right now. It means the governance frameworks I covered earlier — the 63% of organizations that can’t enforce purpose limits on AI agents — now have concrete vendor responses.
Cisco introduced “action control” (shifting from who can access to what agents can do). CrowdStrike launched Charlotte AI AgentWorks. Palo Alto shipped Prisma AIRS 3.0 for the full agentic lifecycle.
The tools now exist. Will the adoption catch up?
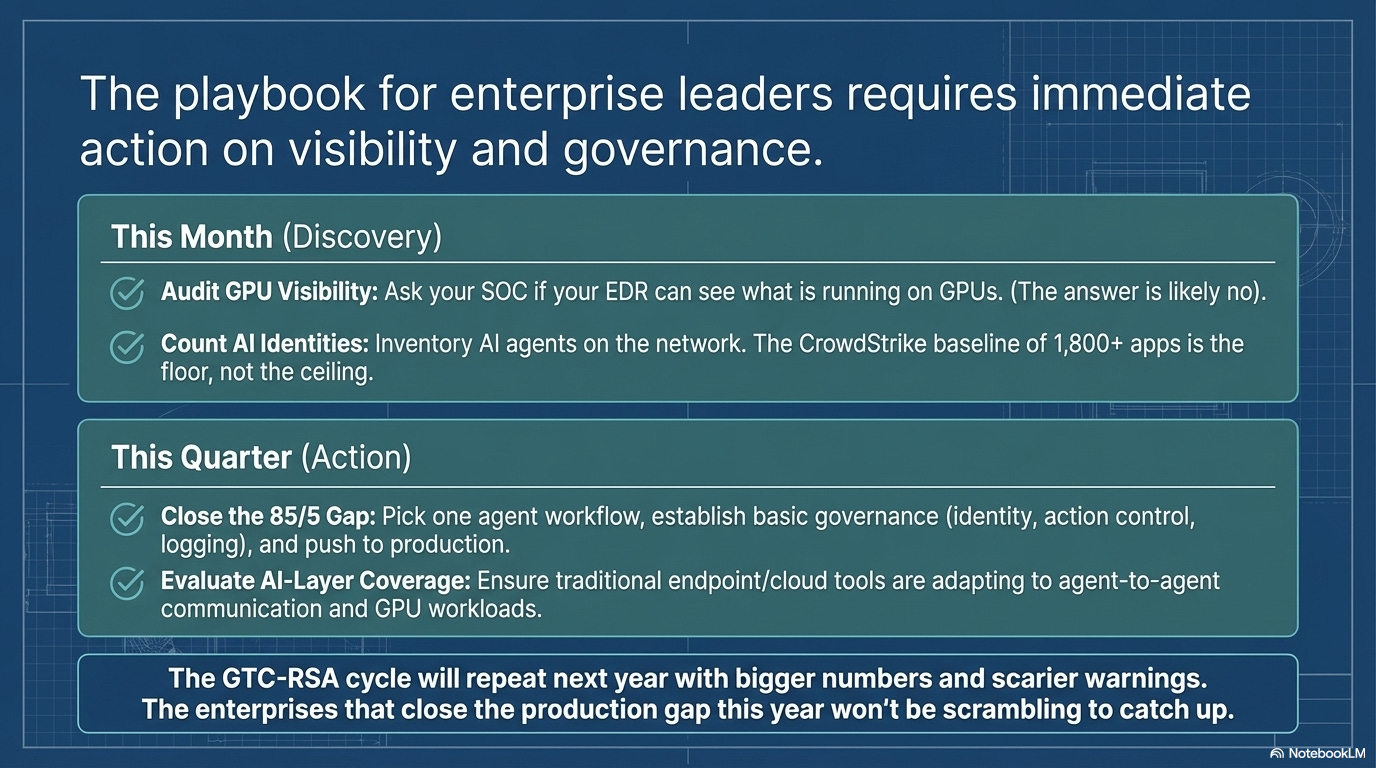
This month:
Audit your GPU workload visibility. Ask your security team: “Can our EDR see what’s running on GPUs?” If the answer is no, (which most likely as this is just emerging) you have a blind spot that didn’t exist two years ago.
Count your AI agent identities. The 82:1 ratio may sound extreme, but most organizations have no inventory of AI agents operating on their network. CrowdStrike’s 1,800+ detected apps across enterprises is the starting point, not the ceiling.
This quarter:
Close the 85/5 gap in your own org. Pick one AI agent workflow, stand up governance (identity, action control, logging), and move it from experiment to production. The governance doesn’t have to be perfect. It has to exist.
Evaluate your security stack’s AI-layer coverage. Traditional endpoint and cloud security tools were not built for GPU workloads or agent-to-agent communication. Geordie AI (RSA Innovation Sandbox winner) and NVIDIA’s DOCA Argus represent two different approaches — startup agility vs. platform integration. Know which bet you’re making.
The GTC-RSA cycle will repeat next year with bigger numbers and scarier warnings. The enterprises that close the production gap this year won’t be scrambling to catch up.
Most of us are in the 85% experimenting, 5% deployed camp. What’s actually blocking the move to production — technical gaps, governance gaps, or the fear of getting it wrong?
References: