2026 Enterprise Guide for AI Control Planes
A 60-day look at the seven vendors selling you the layer that knows what your agents are doing. And the patent fight they’re having about what “knowing” even means.
The scene that’s already happening
Pick a Fortune 500 you know. Walk into a governance committee meeting in May 2026 and ask three questions. How many AI agents are in production right now? Who owns each one? What customer data did agent #34 touch last Tuesday afternoon?
The answer is usually the same. Someone says “we’ll get back to you.” Someone else opens a spreadsheet that hasn’t been updated in six weeks. The number people cite from memory is wrong by a factor of two. Then IT runs the audit. The real count is north of 40. Most of them were spun up by a business team that signed an Agentforce trial. Or by a developer who wired up a Copilot Studio agent to a SharePoint site nobody remembers approving.
This is the scene the AI Control Plane category exists to fix. It’s the layer that’s supposed to answer those three questions in 60 seconds. With audit-grade evidence. Before a regulator or an insurer-customer or a board member asks.
Six of the seven serious vendors hit general availability (GA) inside a 90-day window centered on April 2026. The category went from preview to production in 90 days.
And no two of those seven vendors define what “governance” means the same way.
That’s what I wanted to explore here.
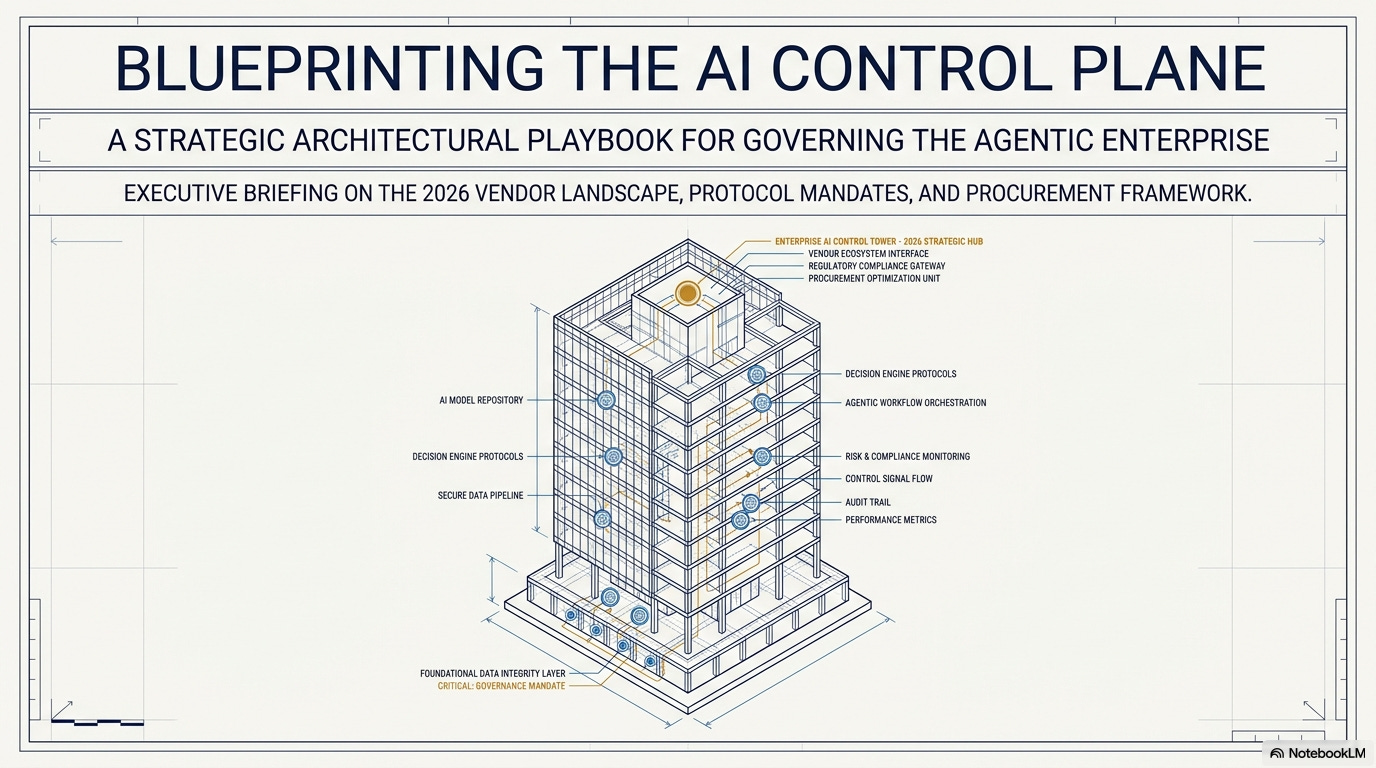
What we’re actually talking about
The analyst firms haven’t reached consensus on this category yet. Gartner, Forrester, IDC, and HFS each have a different explanations. No scored ranking exists that I found. So I’m working off my own definition.
So here’s the working definition I’m using.
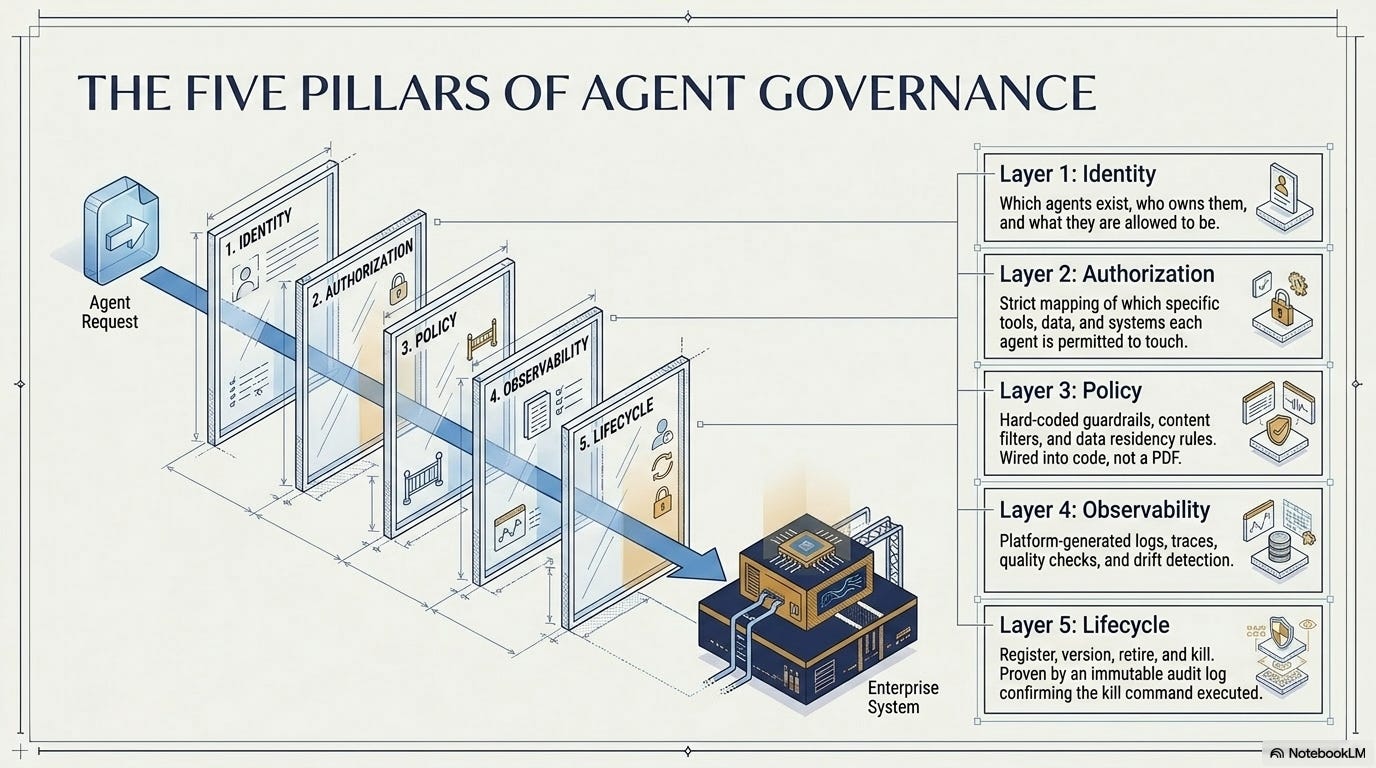
AI Control Plane = the layer that answers five questions about every agent you run:
Identity. Which agents exist. Who owns each one. What each is allowed to be.
Authorization. Which tools, data, and systems each agent is allowed to touch.
Policy. Guardrails, content filters, where data can live, how long it’s kept. Wired into the agent in code, not written in a PDF.
Observability. Logs, traces, quality checks, drift detection, incident response. Generated by the platform, not stitched together by hand.
Lifecycle. Register, version, retire, kill. With proof in the audit log that the kill actually worked.
Out of scope: where agents actually run (the workload sits where the data sits — that’s always fragmented), the model layer (becoming a commodity fast), pure orchestration tools (already a commodity since 2024-2025), and pure RAG.
Why these five? Each one has a test you can run.
For identity: “can the registry tell me how many agents we have, who owns each, and what each is allowed to be — in 60 seconds, yes or no.”
For observability: “for any agent action that touched a customer record yesterday, show me the LLM trace, the policy decision, what the agent did, and where the data came from — in under five minutes, no engineering ticket.”
Each one passes or fails.
The other reason: patent filings show what the vendors really think the category is. Marketing decks are aspirational — anyone can claim anything in a slide. Patents cost real money and take years to file. They’re a vendor’s bet on what’s worth claiming exclusively.
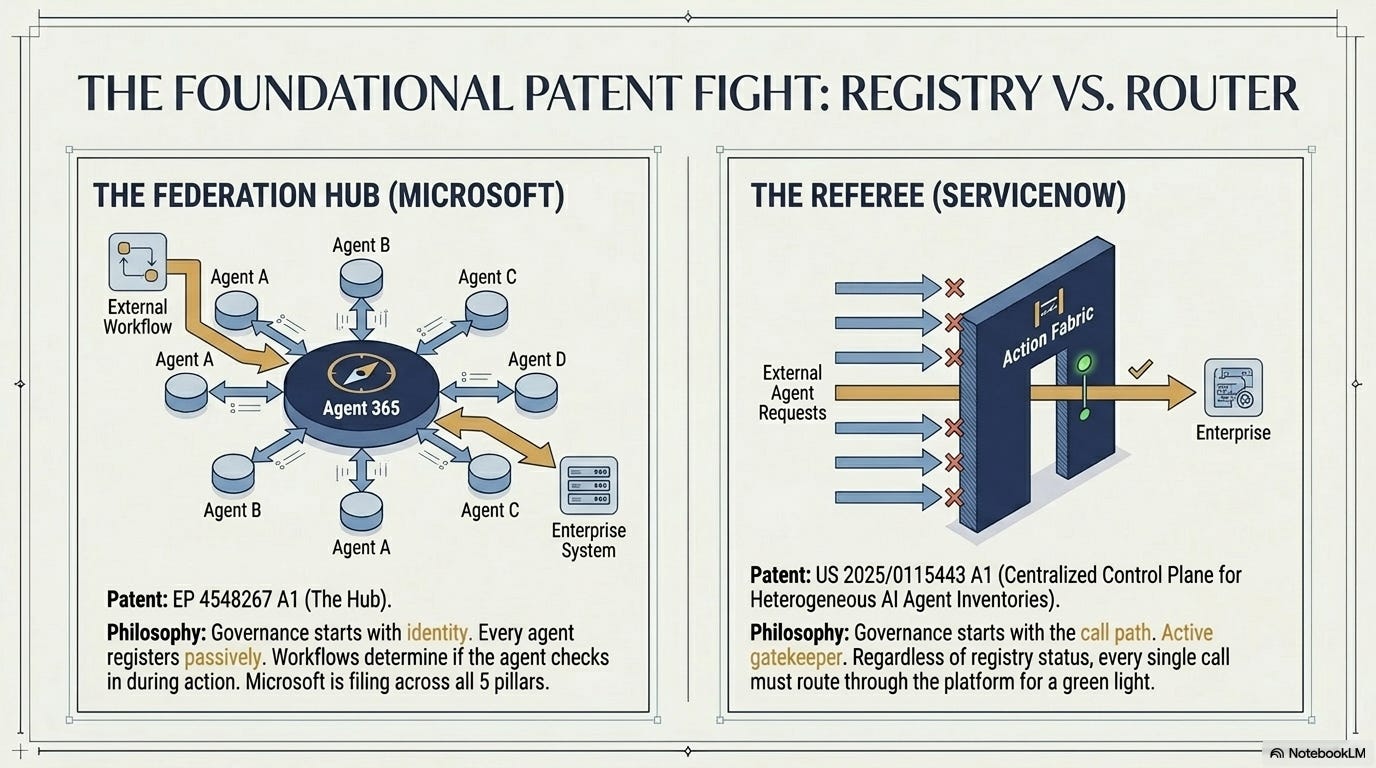
Microsoft is filing across all five pillars. The flagship is EP 4548267 A1, which stakes a claim to Agent 365 as a “federation hub” that other vendors’ agents register into. Around 40+ related filings cover the gateway that sits in front of every agent call, the way the audit log compresses, even how a killed agent gets proven dead.
ServiceNow took a different swing. Their flagship patent (US 2025/0115443 A1) literally claims “Centralized Control Plane for Heterogeneous AI Agent Inventories” — the category name itself, in patent law. Microsoft has filed two to three times as many governance-related patents than ServiceNow.
Two of the biggest enterprise software companies are filing patents on opposite ideas of what governance even means.
Microsoft says governance starts with identity. Every agent registers with us. We’re the directory. Anyone can ask us “what agents do you have, who owns them, what are they allowed to do” — we answer. Whether or not the agent actually checks with us when it acts is up to the workflow.
ServiceNow says governance starts with the call path. Every agent action routes through us. We’re the gate. Before any agent does anything — touches a customer record, calls a tool, hits an API — it has to come to us first for the green light. Whether or not the agent is in our directory matters less than whether the call passes through.
One is a registry (passive, knows what exists). The other is a router (active, sits in the path of every call).
Both could technically coexist. Neither is in their interest.
ELI5 — what’s an AI Control Plane?
Imagine your company hires 47 invisible interns. They each have keys to different rooms. They each touch different files. Nobody wrote down who hired them, what they’re allowed to do, or what they did yesterday.
An AI Control Plane is the building’s front desk. It checks every intern in. It tracks who has which keys. It records who walked into which room. And it has a button to fire any intern that goes off-script.
The vendors below are all selling you a version of that front desk.
The field, at-a-glance
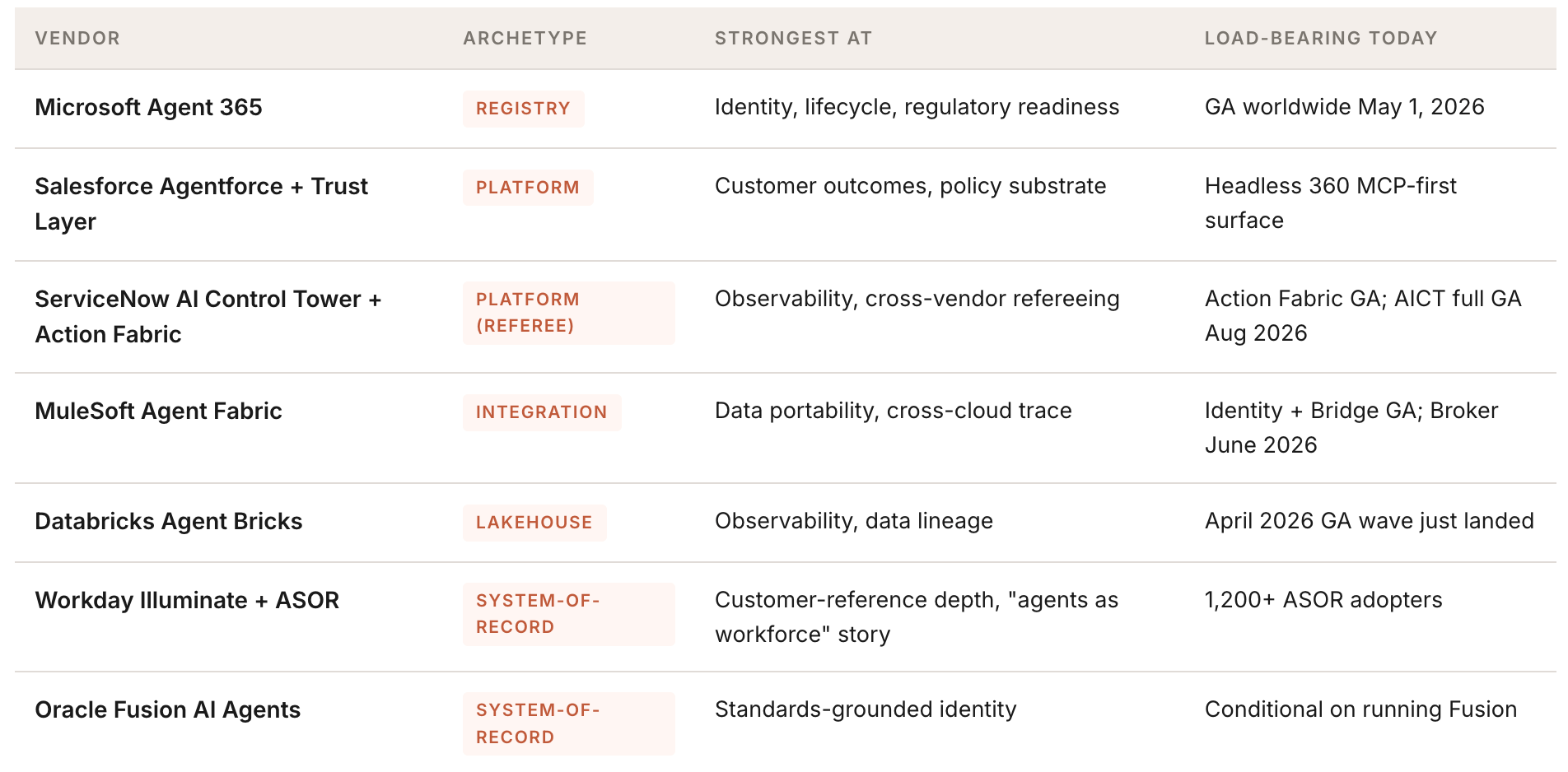
Seven vendors are serious. I scored them against a representative enterprise scale: around 12,000 seats, 2,000 production agents by Year 3, US-primary with UK, EU, and APAC operations, and a regulated-vertical compliance surface.
Seven other vendors are in this space but are really runtime or orchestration tools, not control planes: Glean, Writer, Cohere North, AWS Bedrock AgentCore, Google Agentspace, Palantir AIP, Snowflake Cortex.
I left them out because they do a different job, not because they’re worse.
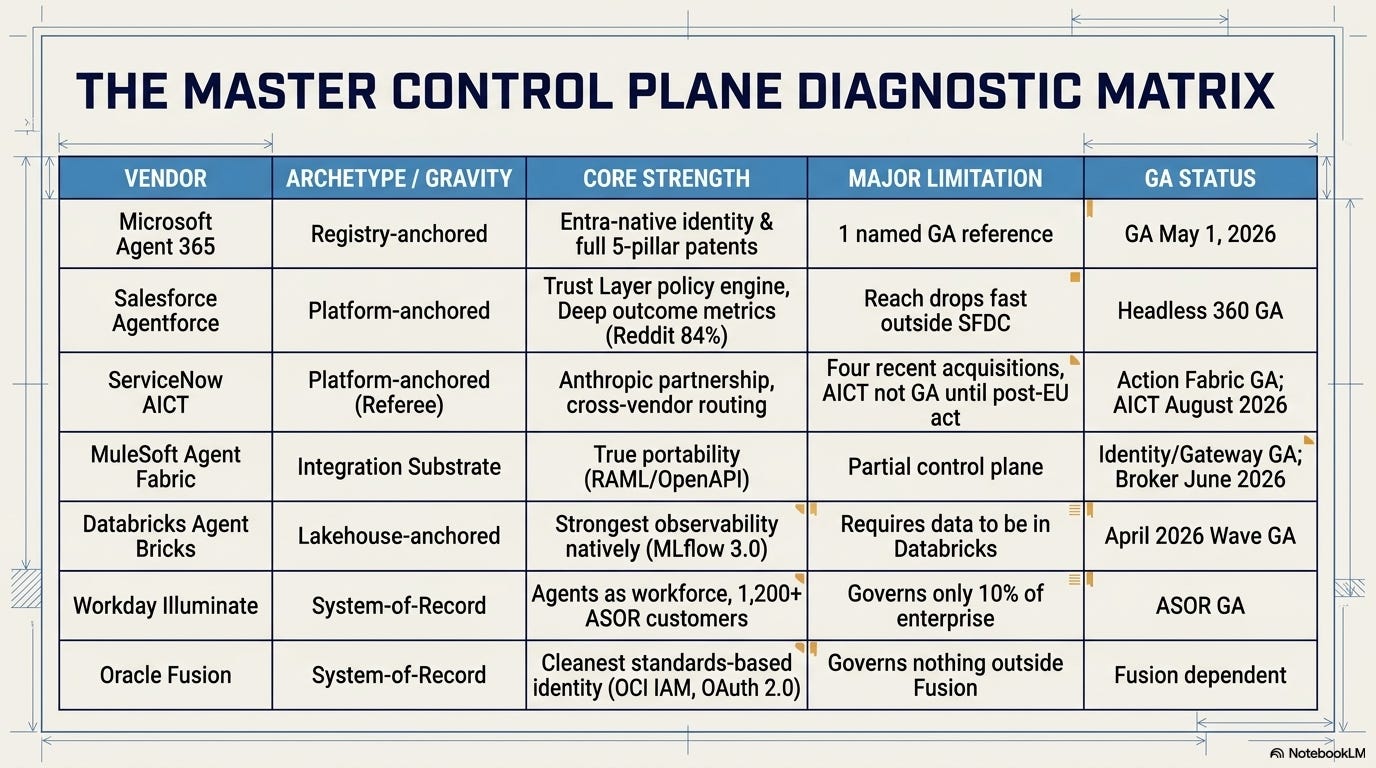
Microsoft Agent 365 is the registry-anchored option. GA worldwide as of May 1, 2026. Available standalone or bundled into a new E7 SKU. Entra Agent ID gives every agent a sponsor, an access package, and a lifecycle that mirrors how humans get governed today. Agent Map shows you the inventory. The patent strategy tells you what Microsoft is really after. EP 4548267 A1 stakes a claim to Agent 365 as the central hub across tenants. Plus 40+ related filings on the gateway, on audit-log compression, on proof that a killed agent stays dead. Microsoft is the only vendor filing across all five pillars. That’s a Year-1 risk for any product this freshly launched.
Strengths:
Entra-native identity — every agent gets the same governance model as humans
GA worldwide today (May 1, 2026), ready to deploy
The only vendor filing patents across all five pillars
Existing M365 + Entra footprint means incremental work, not from scratch
Limitations:
Only one named customer reference at GA (NTT DATA)
Cross-cloud sync to AWS Bedrock and Google Gemini still in public preview
Salesforce Agentforce + Trust Layer is the platform-anchored play with the deepest customer-outcome metrics in the field. Adecco reports 51% off-hours coverage. Reddit reports an 84% cut in resolution time. Trust Layer is Salesforce’s policy engine — the part that decides what an agent is allowed to do, before it does it. It masks personal data before a prompt goes to a model. It blocks responses that break content rules. It logs every prompt and every output. It keeps customer data out of model training, so your data doesn’t end up training somebody else’s AI. Salesforce has patents on how it works, which means competitors can’t just copy the approach. The headline 60-day move was Headless 360, announced at TDX 2026. Agentforce now ships through 60+ MCP tools, working natively in Slack, ChatGPT, Claude, Gemini, Teams. The tradeoff: Trust Layer is strong inside Salesforce. Outside it, the reach drops fast.
Strengths:
Deepest customer-outcome metrics in the field (Adecco 51% off-hours coverage, Reddit 84% faster resolution)
Trust Layer is a mature, patent-defended policy engine
Headless 360 — Agentforce runs through 60+ MCP tools, native in Slack, ChatGPT, Claude, Gemini, Teams
Limitations:
Reach drops fast outside the Salesforce gravity well
Policy engine doesn’t extend cleanly to non-Salesforce systems
Whole strategy is conditional on you staying on Salesforce
ServiceNow AI Control Tower + Action Fabric wants to be the referee. Their pitch isn’t “we govern our agents.” It’s “we govern every agent — Claude, Copilot, OpenAI, custom. Every call routes through us. We check the ID, we set what the agent can do, we keep the audit log, we count what gets used.” The patent claim is US 2025/0115443 A1, covering “Centralized Control Plane for Heterogeneous AI Agent Inventories.“
Action Fabric MCP Server is GA today. The full Control Tower is in Innovation Lab now, with full GA expected August 2026 — after the EU AI Act high-risk deadline. ServiceNow also has the most acquisitions still being absorbed: Moveworks (Dec 2025), Veza (Mar 2026), Armis (closing mid-2026), Traceloop (Mar 2026).
Four products held together by one pitch. All six months old or younger.
Strengths:
Referee model — governs every agent regardless of origin
Patent on the category name itself (US 2025/0115443 A1) — the boldest patent claim in the field
Anthropic (the company behind Claude) helped build it — Claude agents plug into ServiceNow’s governance out of the box
Action Fabric MCP Server is GA today
Limitations:
Full Control Tower not GA until August 2026 — after the EU AI Act high-risk deadline
Four acquisitions still being absorbed (Moveworks, Veza, Armis, Traceloop), all less than six months old
Pitch is more polished than the lived experience right now
MuleSoft Agent Fabric is the integration plumbing nobody outside the architecture community is talking about. And almost everyone needs. Salesforce-owned since 2018. Three pieces are GA today:
Trusted Agent Identity stamps every agent with a verified ID.
Anypoint gateway is the chokepoint that sees every API call and enforces the rules — auth, rate limits, audit logging.
MCP Bridge lets agents that speak MCP (Anthropic’s standard) call any backend API MuleSoft already connects to, without rebuilding the integration.
The fourth piece — Agent Broker, the brain that decides which agent does what — is still in beta, with a June 2026 GA target.
The reason architects care: this is the only one of the seven where you can actually take your work and leave. RAML and OpenAPI definitions and Mule flows transfer to Kong or Apigee if you decide to switch. That’s a rare property.
Strengths:
The only vendor where you can actually take your work and leave (RAML, OpenAPI, Mule flows transfer)
Three components are GA today: Trusted Agent Identity (gives every agent a verified ID), Anypoint gateway (the chokepoint that sees every API call and enforces rules), and MCP Bridge (lets agents that speak MCP call any API MuleSoft already connects to)
Salesforce-owned since 2018 — mature backing, not a startup risk
Limitations:
Partial control plane only — integration governance, no identity/policy/lifecycle on its own
Agent Broker (the orchestration brain) still in beta — GA target June 2026
Has to be paired with another vendor for the full picture
Databricks Agent Bricks is the lakehouse-anchored play. It has the strongest observability story of the seven. Three pieces work together to get there:
MLflow 3.0 records every step an agent takes — like a flight recorder for AI.
Unity Catalog tracks who can access what data and where each piece of data came from.
Mosaic AI Gateway sits in front of every model call, applies the rules, and logs the prompt and the response.
Put them together and you can pull the trace, the policy decision, what the agent did, and where the data came from — natively, no third-party bolt-ons required. The April 2026 GA wave (Supervisor Agent, Document Intelligence, Custom Agents all moved from preview to GA inside the 60-day window) is the biggest wave in the field. If your data already lives in Databricks, this is the conversation. If it doesn’t, the same data-gravity argument works against you.
Strengths:
Strongest observability story of the seven (MLflow 3.0 + Unity Catalog + Mosaic AI Gateway)
Pulls the trace, the policy call, the agent action, and the data lineage natively — no glue
Three major modules just moved to GA in April 2026 (Supervisor Agent, Document Intelligence, Custom Agents)
Limitations:
Only the right answer if your data already lives in Databricks
Weak coverage for productivity agents (Teams, Slack, browser)
The same data-gravity argument that helps you here hurts you if your data lives elsewhere
Workday Illuminate + Agent System of Record (ASOR) has the cleanest story in the seven-vendor set: agents are workforce members. Same ID model as humans. Same access setup. Same lifecycle. Onboard, scope, audit, deactivate. ASOR has 1,200+ customers using it today. The catch: ASOR only governs agents that live inside Workday’s HR and Finance footprint. That’s maybe 10% of the agents in a typical enterprise.
Narrow reach, but deep clarity inside that reach. A real tradeoff.
Strengths:
Cleanest story of the seven — agents are workforce members, with the same ID/access/lifecycle as humans
1,200+ ASOR customers today — the deepest customer-reference base in the field
Deep clarity and operational maturity inside HR and Finance
Limitations:
Only governs agents inside Workday’s HR and Finance footprint
Roughly 10% of a typical enterprise’s agent population
Has to be paired with another vendor for the other 90%
Oracle Fusion AI Agents is the conditional. If you run Oracle Fusion, this conversation is real. Oracle quietly has the cleanest identity story of the seven, built on actual standards instead of proprietary glue. Three pieces stacked together:
OCI IAM — Oracle’s identity service. The directory of who has access to what.
OAuth 2.0 — the open standard that lets a service get permission to act on a user’s behalf (the same protocol behind “Sign in with Google”).
JWT Bearer with User Assertion — a specific flow where the agent presents a signed token that says “I’m acting for user X, here’s what they let me do.”
Oracle followed the published specs exactly — no proprietary extensions — and wrote it up at engineering depth in their own blogs. That matters because another system can verify an Oracle agent’s identity using public standards. You’re not locked into Oracle’s stack just to make agents work elsewhere.
If you don’t run Fusion, Oracle is governing nothing for you and you can skip the rest. The customer-reference base is thin. TIM Brasil — a Brazilian telecom — is the only one they cite publicly.
Strengths:
Cleanest standards-based identity story of the seven (OCI IAM + OAuth 2.0 JWT Bearer + User Assertion)
Built on open standards, not proprietary glue
Documented at engineering depth in Oracle’s blogs — not vaporware
Limitations:
Governs nothing outside Oracle Fusion
Skip the rest of this section if you’re not on Fusion
Thin customer-reference base (TIM Brasil is the named anchor)
ELI5 — what’s an “archetype”?
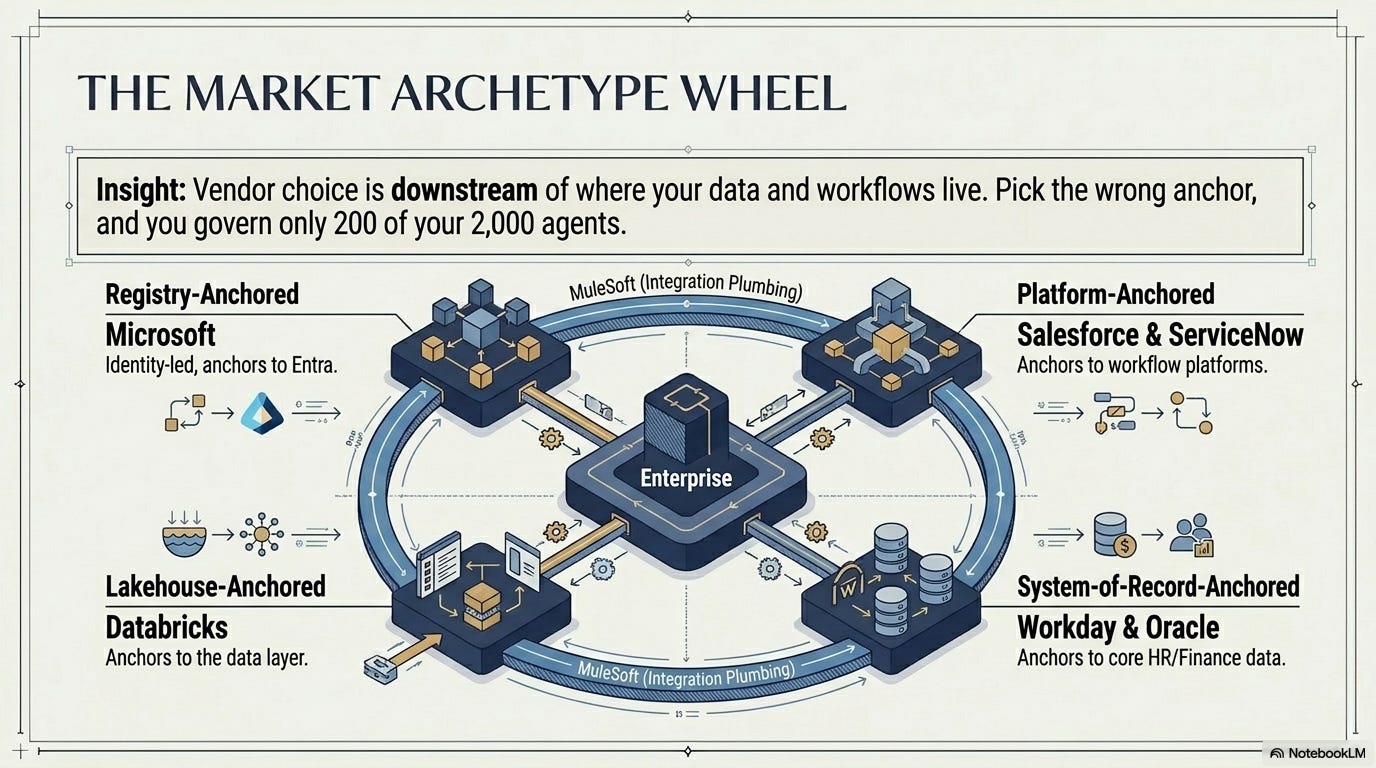
Each of these seven vendors is anchored to a different gravity center. Where does your data live? Where do your workflows live? Whoever owns that gravity center is trying to extend their reach into agent governance.
Microsoft anchors to identity (every agent is a user in Entra). Salesforce and ServiceNow anchor to their platforms. Databricks anchors to the lakehouse (the data). Workday and Oracle anchor to systems-of-record (HR, Finance). MuleSoft is the integration plumbing.
The archetype matters more than the brand. Pick the wrong anchor and you’ll be governing 200 of your 2,000 agents.
Where they actually diverge
At least at this point, I haven’t seen any of this discussed in the vendor whitepapers or analyst reports. Every finding below cuts against at least one vendor’s pitch — which is probably why.
5 things matter once you look past the surface. The buying decision comes down to them.
1. There’s a patent fight about what the category is.
Microsoft and ServiceNow have filed patents that describe two different architectures.
Microsoft’s EP 4548267 A1 describes a federation-hub model. Agent 365 sits at the center. Agents from other vendors register their information into the Microsoft directory through cross-cloud sync. Sync to AWS Bedrock and Google Gemini Enterprise is in public preview as of May 2026.
ServiceNow’s US 2025/0115443 A1 describes a referee model. Action Fabric sits in front of every enterprise agent, regardless of where the agent came from. AICT handles the routing, the audit, and the metering.
The two patent libraries aren’t the same size. Microsoft has filed two to three times more governance-related patents than ServiceNow. ServiceNow’s flagship patent claims the category name itself.
You should care because this isn’t a feature comparison. It’s a disagreement over what governance even means. Pick the wrong architecture for where your data and workflows live, and you’re not making a bad procurement call — you’re making a bad architecture call that takes years to undo.
2. There are four control-plane archetypes, not seven vendors.
Lakehouse-anchored (Databricks; Snowflake Cortex if you swap one for the other).
Registry-anchored (Microsoft).
Platform-anchored (Salesforce, ServiceNow).
System-of-record-anchored (Workday, Oracle).
Vendor choice is downstream of which archetype fits your data-and-workflow gravity center, not the other way around.
Two patterns show up in practice. Some companies pick a vendor first and work out which archetype fits afterward. Others name their gravity center first (we are a Workday-and-Salesforce shop with Microsoft 365 at the floor) and then ask which archetypes work inside that.
The second order tends to produce architectures that hold up across refresh cycles.
Most enterprises run two archetypes, sometimes three. Microsoft for the productivity-anchored agents and the registry. Workday or Oracle for HR and finance agents. Databricks or Snowflake for the data-native agents. Salesforce or ServiceNow for the agents inside their platforms.
The single-vendor story shows up in pitches more often than in production stacks. The practical question is which two or three vendors will end up in your architecture, and how they talk to each other.
3. Scope coverage varies by 10x across these vendors.
This was the divergence point that took me longest to see clearly as I dug into the vendors. Two vendors govern your whole agent population. Two govern a slice. The rest sit somewhere in between. If you read the vendor decks, every one of them sounds like it covers everything. They don’t.
Workday Illuminate governs the agents living inside HR and Finance. In a typical enterprise that’s maybe 10% of the agent population. Oracle Fusion AI Agents has the same shape — strong inside Fusion, governs nothing outside. MuleSoft Agent Fabric is integration governance only: no identity, no policy, no lifecycle on its own. It’s a partial control plane by design.
Microsoft Agent 365 and ServiceNow AICT are the two that can credibly reach across the whole enterprise.
Microsoft because Entra already holds every human identity — extending to agents is an extension problem, not a from-scratch one. ServiceNow because Action Fabric routes calls no matter where the agent came from. Salesforce sits in the middle: strong inside Salesforce, real reach into Slack and Teams via Headless 360, but the policy engine doesn’t extend cleanly to non-Salesforce systems. Databricks is the same shape, just anchored to the lakehouse instead.
What this means, taken with #2: the company-wide governor and the domain governor are two different jobs.
One sets the registry, the policy rules, the audit spine. The other does the deep work inside HR or finance or the data warehouse — HR agents need to see HR data, finance agents need to trace finance flows. Asking either type of vendor to do the other’s job is where most pilots stall. The audit logs don’t match up. The identity models don’t line up.
Six months in, you’re rebuilding a piece you thought you’d already bought.
ELI5 — why scope matters more than the vendor name
Picture a 2,000-person company. Each “person” is an AI agent. Some sit in HR. Some sit in customer service. Some sit in the data warehouse. Some sit in Microsoft Teams.
No single vendor watches the whole building. Workday only watches the HR floor. Databricks only watches the data team. Microsoft and ServiceNow watch the lobbies and corridors.
So before you ask “which vendor is best,” ask “which floors of my building does this vendor actually watch.” Anyone selling you a single-vendor answer for the whole building is leaving floors unwatched.
4. Anthropic is connective tissue across three of the seven.
This one surprised me and then it made sense. Anthropic is the named design partner for ServiceNow’s Action Fabric. Anthropic powers MCP Apps in Salesforce and Slack. Slack-in-Claude and Agentforce-in-Claude both ship through Anthropic’s surface. Anthropic-backed agents are explicitly governed by Microsoft Agent 365 on Windows endpoints.
The model layer is supposed to be commoditized. In practice, one model provider is wired into the governance fabric of three of the largest control-plane vendors. If Anthropic’s posture shifts on any of those partnerships, the dynamics underneath three vendor stories move at the same time. This is worth tracking for procurement reasons, not just architectural ones.
5. MCP has won as the protocol. A2A is uneven. AGNTCY is absent.
The protocol fight that was supposed to be three-way isn’t three-way anymore.
Model Context Protocol (run by Anthropic, with a multi-vendor steering committee since 2025) is now the standard everybody ships first for agent-to-tool calls. Microsoft, Salesforce, ServiceNow, MuleSoft, Databricks all have native MCP.
Google A2A (agent-to-agent communication) is named by some, deferred by others, uneven across the seven.
AGNTCY (a way to prove an agent’s identity using a separate ID standard) isn’t in any of the seven vendors’ production stack yet.
What buyers should do: make MCP support a hard requirement in your RFP. Treat A2A as a roadmap question, not a today question. Don’t pay extra for AGNTCY today. Revisit in 12 months.
ELI5 — MCP, A2A, AGNTCY (the three protocol acronyms)
Think of these as three competing standards for how agents talk to each other and to your tools.
MCP (Anthropic’s standard) is how an agent calls a tool. Like USB-C for AI. It already won. Every major vendor ships it.
A2A (Google’s standard) is how two agents talk to each other. Still half-built. Some vendors named it. Most are quiet.
AGNTCY is how an agent proves it’s a real agent (not a fake one). Nobody’s shipping it yet. Don’t bet on it this year.
Bottom line: demand MCP support. Don’t pay extra for the other two.
A decision frame, if you’re a CIO or CTO
Five questions, in this order. The order matters more than the answers.
Q1 Is the category mature enough to commit?
The pillars — identity, authorization, policy, lifecycle are mature enough. Every vendor in scope scores 3-of-5 or higher on the pillar rubric. The federation question (does Microsoft’s hub model win?) and the broker question (does ServiceNow’s referee model win?) are not mature.
My read: 30-40% chance the hub model consolidates the field in 24 months. 15-25% chance the referee model does. 40-55% chance things stay fragmented. The most likely outcome is “no winner.”
Commit to the pillars. Hedge on the hub-vs-referee question. Don’t bet your architecture on either model becoming the default.
Q2 Is your governance maturity ready?
If you are like most enterprises, you probably land at a 1.5-2.0 maturity score across the five pillars when an agent governance program starts. On a 1-5 scale, where 3 is “we can run this reliably” and 4 is “we can run this at scale.” The 12-month target should be 3.0. The 24-month target 4.0. Getting from 1.5 to 3.0 in 12 months takes four specific hires before you scale the pilot: an AI Ops Lead, two Agent SREs, an Agent PM, a Policy Engineer.
Those four roles are also going to be the most-fought-over 2026 hires in this space — second reason to start hiring before you start buying.
Q3 Is your stack constrained?
Yes, and the constraint should shape the recommendation, not be ignored. If you run Microsoft 365 underneath everything (most enterprises do), the registry-anchored option starts ahead because Entra already governs every human ID. Extending it to agents is an add-on, not a from-scratch project.
If you run a real Databricks footprint, the lakehouse-anchored option for data-heavy agents starts ahead. Throwing away what you already paid for is usually a mistake — and an expensive one. Constraints make the answer simpler, not worse.
Q4 Is the regulatory clock running out?
The EU AI Act’s high-risk rules turn on August 2, 2026. About 11 weeks from now. If you’re a financial services firm, a healthcare firm, or sell tools to firms in regulated industries, you’re exposed indirectly but really. Your customers will ask for Article 11 audit evidence as part of their own audits. NAIC’s rules now cover 24 US states. New York’s Circular Letter No. 7 and Colorado’s Reg 10-1-1 are stricter still. EIOPA’s 2027 priorities call out broker AI tools by name. The regulatory clock rules out any vendor whose core pieces aren’t GA today. That’s why ServiceNow AICT (full GA in August 2026) and MuleSoft Agent Broker (GA in June 2026) wouldn’t make my shortlist for a deadline-driven pilot today — even though both look architecturally credible.
Q5 Is the talent available?
Partially. The market for Agent SREs and AI Ops engineers is heating up fast in major US cities and London through 2026 and the comp bands are widening every quarter. The four roles a serious pilot needs can be filled in 6-9 months from a Q3 start. Vendor certifications (MS-102, AI-102, Workday Pro, Databricks GenAI Eng) give you a way to retrain existing EA team members in parallel. Systems integrators with real Agent Ops experience (Accenture, KPMG, Deloitte are the three Microsoft Agent 365 launch partners with the deepest bench) cover the gap in Year 1.
The talent problem is solvable. But only if you start hiring before, not after, you sign the vendor contract.
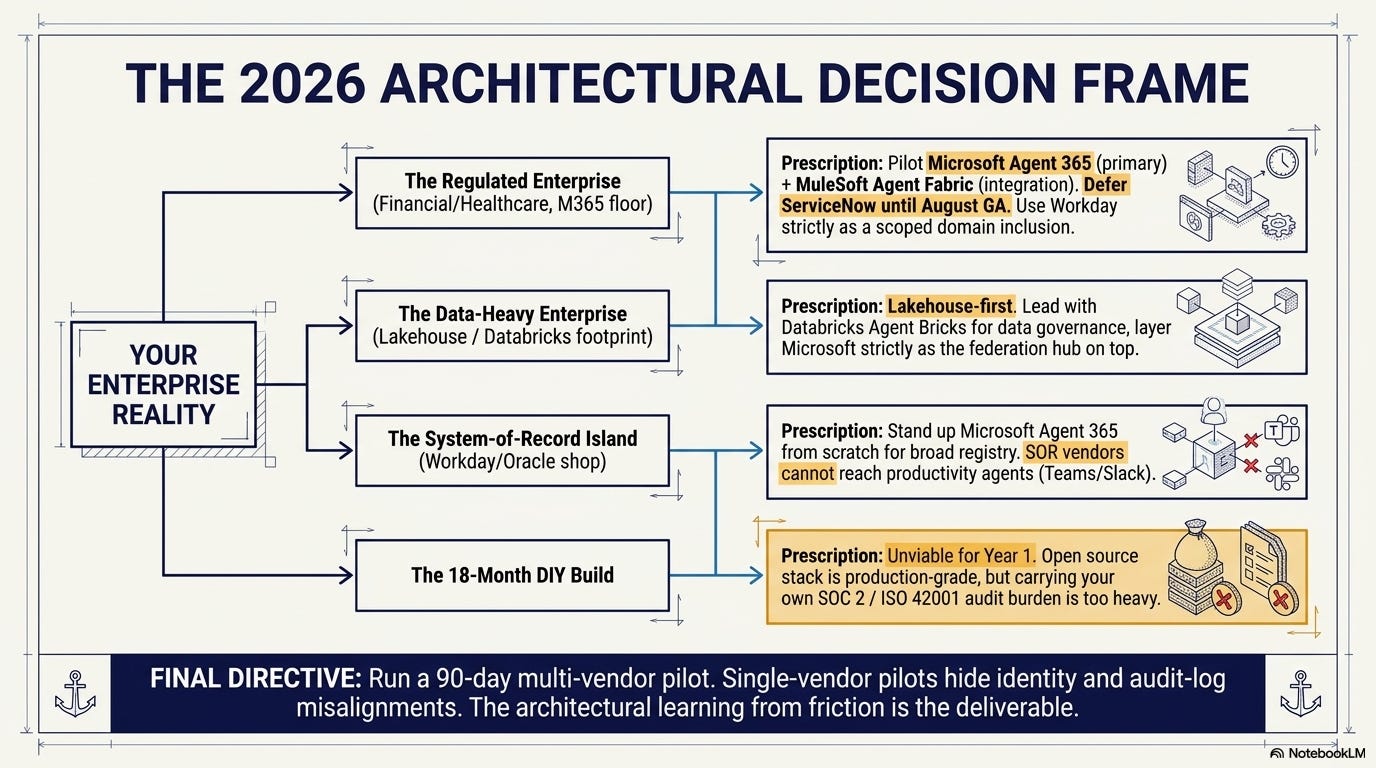
Where the five answers land
If you’re regulated, stack-constrained, and at CMMI 1.5-2.0 (which describes most enterprises in financial services, insurance, healthcare): pilot Microsoft Agent 365 as primary, paired with MuleSoft Agent Fabric’s GA-today components for cross-vendor integration governance, scoped to the regulatory deadline. Defer ServiceNow AICT for a refresh after its August GA. Hold Salesforce conditional on whether you’re staying on Salesforce. Use Workday Illuminate as a scoped Year-1 inclusion for HR-finance agents only, not as a primary. That’s the architecture that survives all three category scenarios (federation-hub winning, referee winning, fragmentation persisting) without rebuilding.
If your data lives in a lakehouse and you already run Databricks: lakehouse-first, with Microsoft as the federation layer on top. Databricks ends up governing more of your agent population than a registry-first read would suggest.
If you’re a Workday-and-Oracle shop with no Microsoft to build on: this is the hardest pattern in the field. Both system-of-record vendors govern their own turf cleanly. Neither reaches the productivity-anchored agents (Teams, Slack, browser). Standing up Microsoft Agent 365 from scratch may still be the answer, even without the bundle discount. There’s no system-of-record vendor in the field with a registry broad enough to govern the rest.
If you can wait 18 months and run a serious DIY effort: the build option is viable.
The open-source stack — MCP plus LangFuse plus Arize Phoenix plus OPA/Rego plus a custom registry on top of your existing identity provider — is production-grade in 2026.
The reason almost no enterprise is choosing this path is the audit problem. Vendors carry SOC 2, ISO 27001, ISO 42001 — their certifications flow through to your customers as evidence. If you build it yourself, you have to certify it yourself. That’s a much bigger lift than the engineering number suggests. The build option is a Year-2 conversation, not a Year-1 one.
A multi-vendor pilot would be my recommendation. Pilot two vendors in parallel for 90 days against the same use cases. The two pilots will surface things that don’t line up (identity, authorization, audit-log shape) that a single-vendor pilot hides.
The architectural learning is huge.
So pick the maturity step, not the vendor
This isn’t a tools comparison, even though I just spent 4,000 words ranking tools. The thing actually being chosen here is which governance maturity step your organization is working on this quarter. Standing up an identity registry? Wiring policies into the agents? Getting trace lineage to work end to end? Federating across vendors?
Each step maps to a different vendor strength and a different paired-platform decision. The vendor question follows the maturity question, not the other way around.
The pattern I’ve seen work: name the step first, then pick the vendor. Write the success criteria, run a 90-day pilot against the criteria, and only then commit. The pattern I’ve seen struggle: pick the vendor first, get into procurement, and back-fill the maturity story to justify the choice.
Honestly, I don’t always spot the difference quickly, but it usually surfaces inside the first strategy conversation.
Pick the maturity step you’re working on next. Then ask which two of these seven vendors actually move it in 90 days. That’s the buying decision.
Next month: what each of these vendors actually costs at 2,000-agent scale. The number is bigger than the demos suggest. The bill is mostly not the seat license.